关联漏洞
标题:Dasan GPON家庭路由器命令注入漏洞 (CVE-2018-10562)Description:Dasan GPON是韩国Dasan公司的一款家用路由器产品。 Dasan GPON家庭路由器中存在命令注入漏洞,该漏洞源于用户再次访问/diag.html页面时路由器将因特网包探索器的结果保存在/tmp中并将它传输给用户。攻击者可通过向GponForm/diag_Form URI发送带有‘dest_host’参数的diag_action=ping请求利用该漏洞执行命令并检索输出。
Description
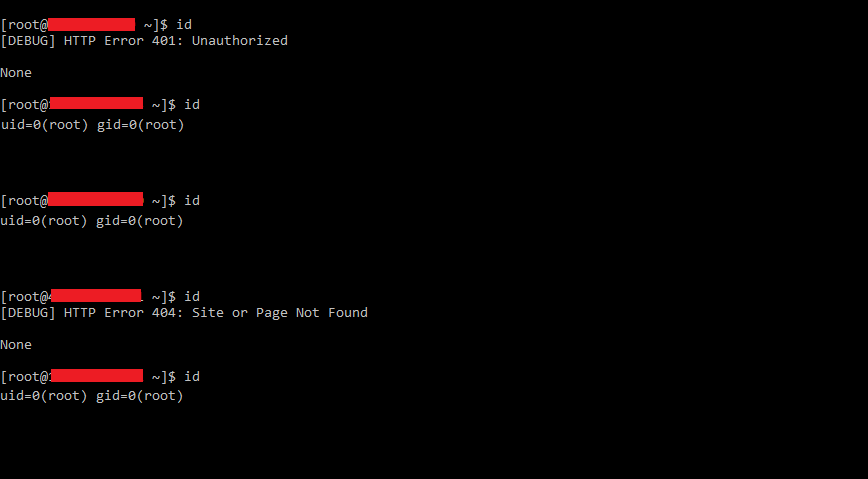
Exploit for Mass Remote Code Execution on GPON home routers (CVE-2018-10562) obtained from Shodan.
介绍
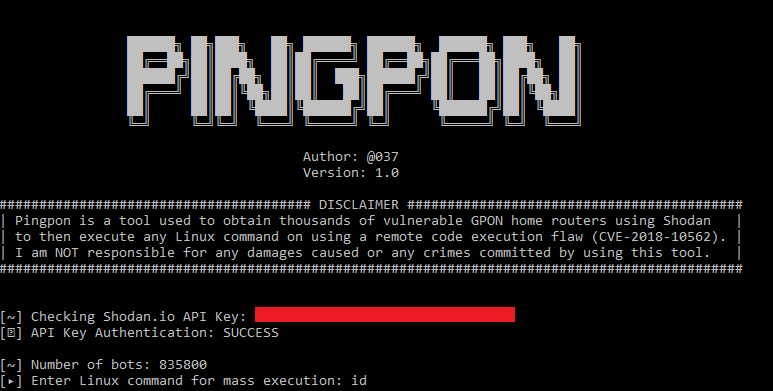
# PINGPON EXPLOIT
* Author: [@037](https://twitter.com/037)
Pingpon is a tool used to obtain thousands of vulnerable GPON home routers using Shodan.io to then execute any Linux command on using a remote code execution flaw (CVE-2018-10562).
## DISCLAIMER
I am NOT responsible for any damages caused or any crimes committed by using this tool.
Original Script: [github.com/f3d0x0/GPON](https://github.com/f3d0x0/GPON)
### Prerequisites
You're required to install Python 3.x
```
apt-get install python3
```
You also require to have the Shodan and Request modules installed
```
pip install shodan
```
```
pip install requests
```
### Using Shodan API
This tool requires you to own an upgraded Shodan API
You may obtain one for free in [Shodan](https://shodan.io/) if you sign up using a .edu email
文件快照
[4.0K] /data/pocs/1b1246fec6d5bfee80b15e96224eff1f12432d7b
├── [ 16K] 1.png
├── [ 10K] 2.png
├── [3.7K] Pingpon.py
└── [ 972] README.md
0 directories, 4 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。