关联漏洞
Description
Verify if your installed version of xz-utils is vulnerable to CVE-2024-3094 backdoor
介绍
# xz-backdoor-CVE-2024-3094-Check
Verify if your installed version of xz-utils is vulnerable to CVE-2024-3094 backdoor. This check is for Kali Linux or other Debian based installs.
## Usage
```
git https://github.com/Bella-Bc/xz-backdoor-CVE-2024-3094-Check.git
cd xz-backdoor-CVE-2024-3094-Check
chmod +x check_xz_utils_CVE-2024-3094.sh
./check_xz_utils_CVE-2024-3094.sh
```

## References
https://www.kali.org/blog/about-the-xz-backdoor/ <br><br>
https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27<br><br>
https://arstechnica.com/security/2024/04/what-we-know-about-the-xz-utils-backdoor-that-almost-infected-the-world/
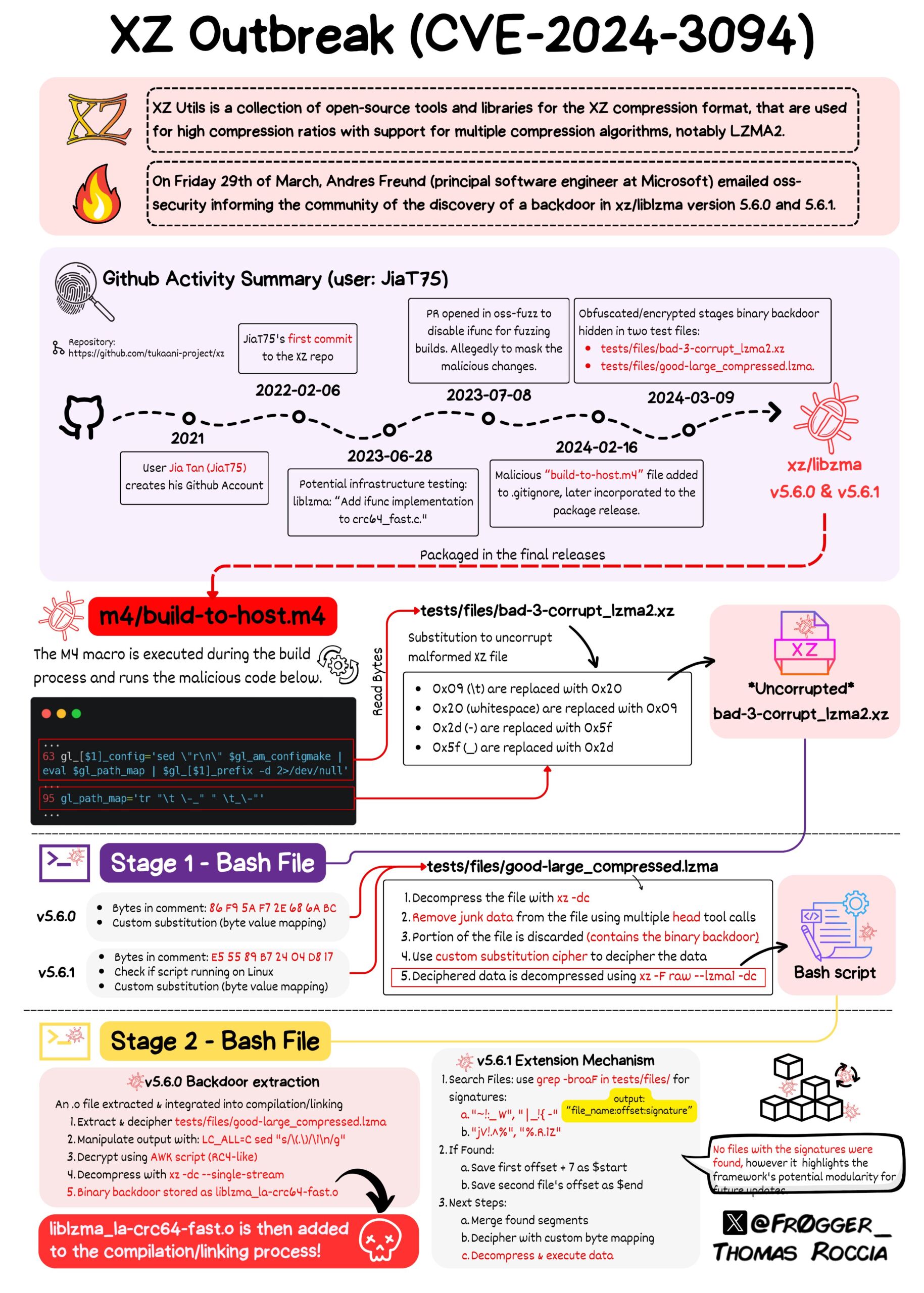
## CVE Overview
文件快照
[4.0K] /data/pocs/2446f2400044169b761144a3c536cc41d761dfd0
├── [ 662] check_xz_utils_CVE-2024-3094.sh
└── [ 912] README.md
0 directories, 2 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。