Clario through 2024-04-11 for Windows Desktop has weak permissions for %PROGRAMDATA%\Clario and tries to load DLLs from there as SYSTEM.# CVE-2024-34474
Clario through 2024-04-11 for Windows Desktop has weak permissions for %PROGRAMDATA%\Clario and tries to load DLLs from there as SYSTEM.
### Description:
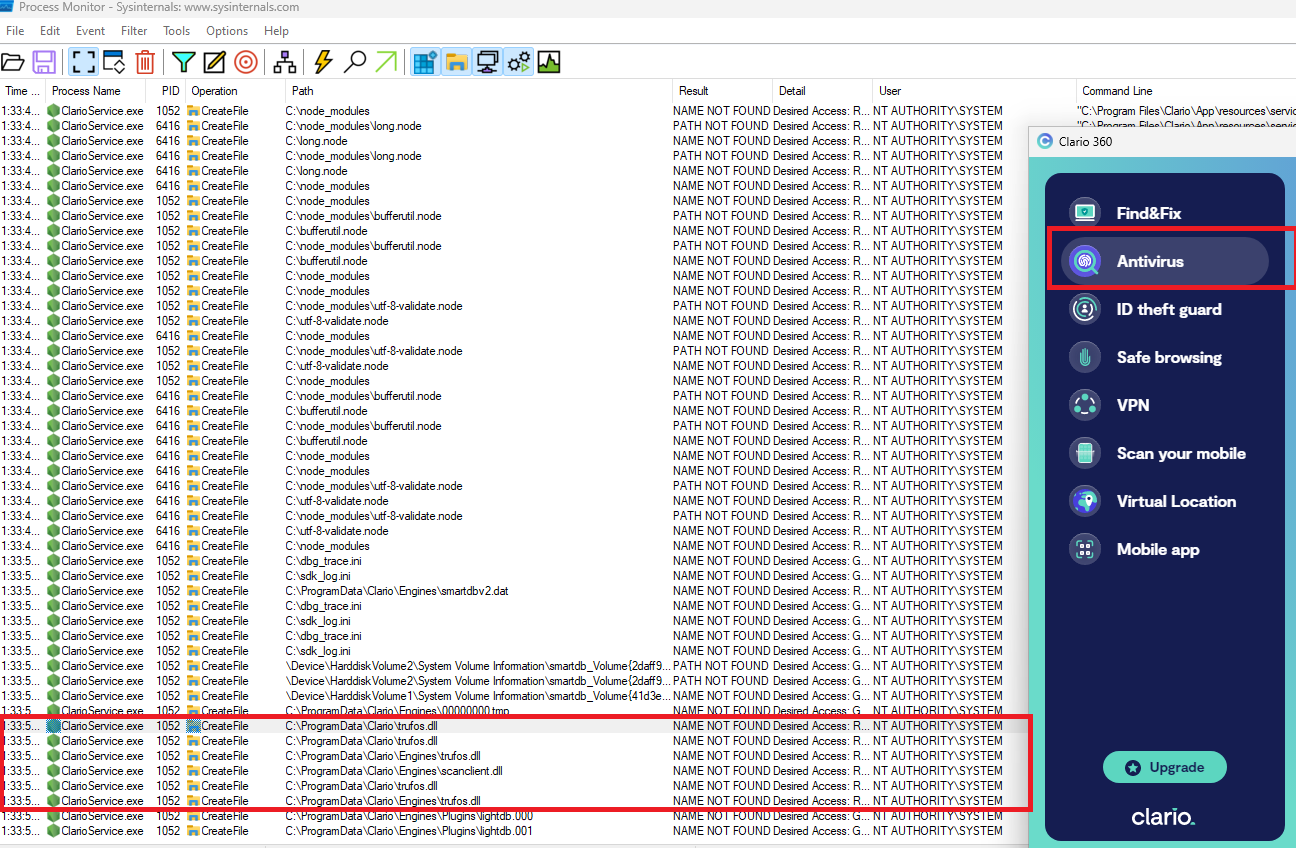
Clario for Windows desktop application attempts to load non existent DLLs libraries from C:\ProgramData\Clario\ and C:\ProgramData\Clario\Engines\ when a user performs an Antivirus scan. The DLL files do not exist and this process is invoked with SYSTEM privileges even if a non admin performs it. By default, on windows systems, any authenticated users can create files/Folders under the c:\ProgramData\Clario path. A user with low privileges can create the DLL files under C:\ProgramData\Clario\ and C:\ProgramData\Clario\Engines\ to execute arbitrary code of their choice resulting in elevation of Privileges to the SYSTEM rights.
### Affected versions
Clario versions through 2024-04-11
### Impacted service(s)
Insecure Folders:
C:\ProgramData\Clario\ & C:\ProgramData\Clario\Engines\
Service:
ClarioService.exe
### DLL loaded from world-writable directory
#### Discovered by:
Alaa Kachouh
[4.0K] /data/pocs/0880f5e1a18833efd71dcfa5e58d8fc5cb7298b7
├── [302K] DLLs-not-found.png
└── [1.1K] README.md
0 directories, 2 files