CVE-2019-0859 1day Exploit# CVE-2019-0859-1day-Exploit
CVE-2019-0859 1day Exploit
Target OS : Windows 7 x64 ServicePack1 (7601)
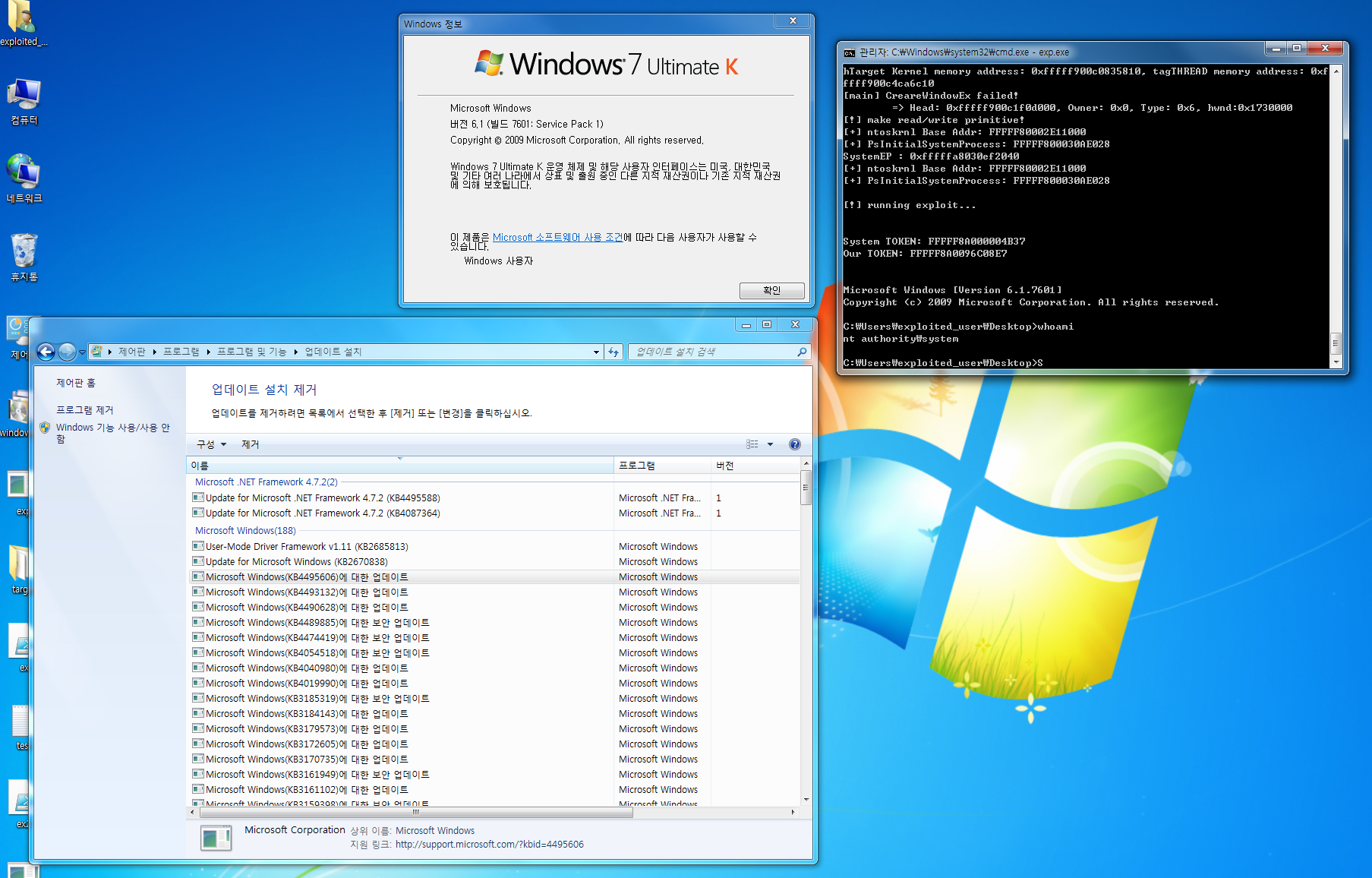
This exploit need to enviroment that is updated with 2019 March security update. Previous update didn't check currently.
exploit relible isn't 100%. Sometime exploit didn't work perfecty. Then you try again...
[4.0K] /data/pocs/0b65d500785e17684d4ccde230613c90eb7883ad
├── [2.6M] CVE-2019-0859 1day Exploit.pdf
├── [4.0K] exp
│ ├── [4.0K] exp
│ │ ├── [ 38K] exp.cpp
│ │ ├── [5.2K] exp.h
│ │ ├── [8.6K] exp.vcxproj
│ │ ├── [1.5K] exp.vcxproj.filters
│ │ ├── [ 162] exp.vcxproj.user
│ │ ├── [ 380] stdafx.cpp
│ │ ├── [ 450] stdafx.h
│ │ ├── [ 142] syscall_x64.asm
│ │ ├── [ 629] syscall_x64.h
│ │ └── [ 452] targetver.h
│ └── [1.4K] exp.sln
└── [ 427] README.md
2 directories, 13 files