# CVE-2022-32074 for osTicket | Support Ticketing System
```
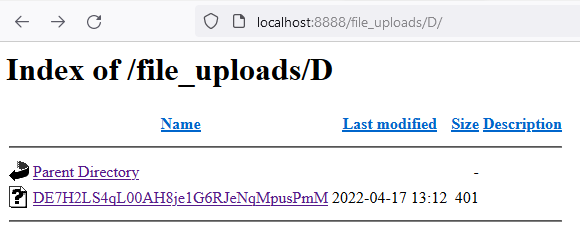
1. Find the file listing directory, the root of the file download directoryм (file_uploads (this is an example)).
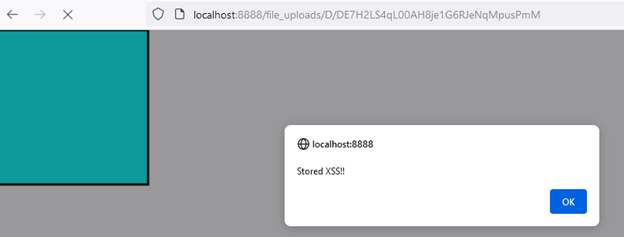
2. Load the following xssPayload.svg and open it
```
Example:
[4.0K] /data/pocs/20864c2d50a981fc07ff1e81246f7106c58b1c94
├── [ 16K] cve2.png
├── [ 14K] cve.png
├── [ 404] README.md
└── [ 394] xssPayload.svg
0 directories, 4 files