CrushFTP before 11.3.7_60 is vulnerable to HTML Injection. The Web-Based Server has a feature where users can share files, the feature reflects the filename to an emailbody field with no sanitzations leading to HTML Injection.# CVE-2025-63419
CrushFTP before 11.3.7_60 is vulnerable to HTML Injection. The Web-Based Server has a feature where users can share files, the feature reflects the filename to an emailbody field with no sanitzations leading to HTML Injection.
# CWE
CWE-79 — Improper Neutralization of Input During Web Page Generation (Cross-site Scripting)
# CVSS v3.1 Base Score: 3.5 (Low)
```bash
CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:N/I:L/A:N
```
# Summary
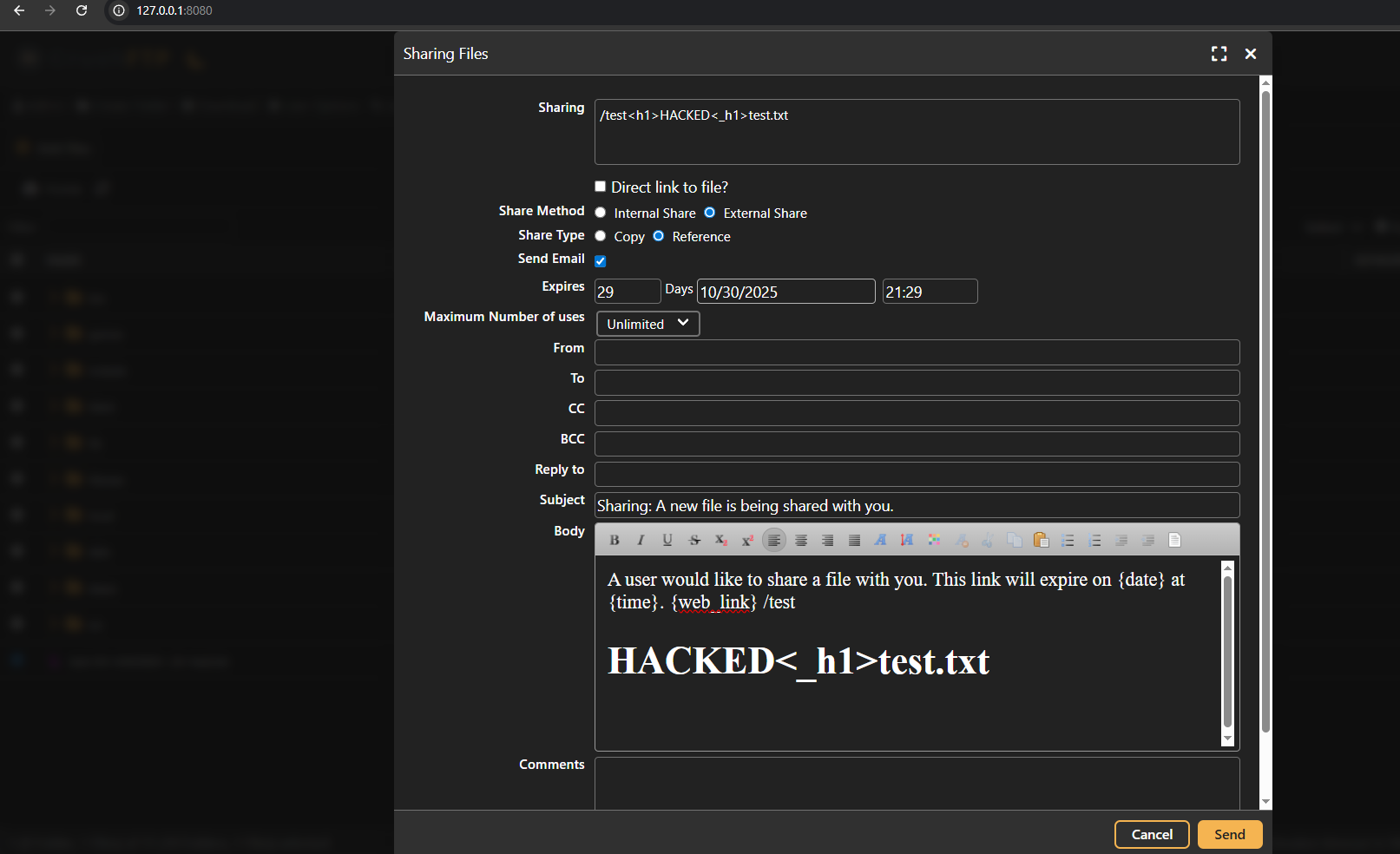
The CrushFTP Web-Based Server has a feature where users can share files, the feature reflects the filename to an emailbody field with no sanitzations leading to HTMLi, While the feature intentionally supports limited HTML code usage, lack of sanitzations makes this injection unintentional and poses a low integrity impact.
# Steps to reproduce
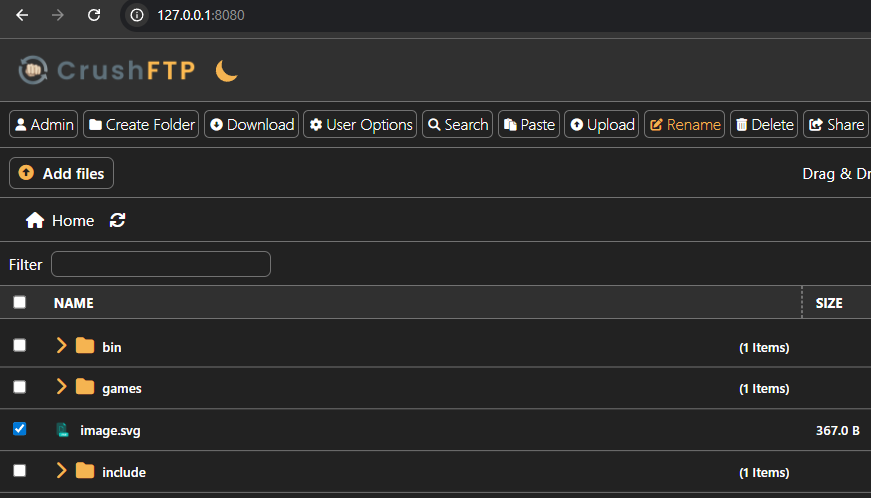
1. Navigate to http://127.0.0.1:8080/
2. Select a file ( Just incase there are no files an attacker must upload one and then proceed with the other steps )
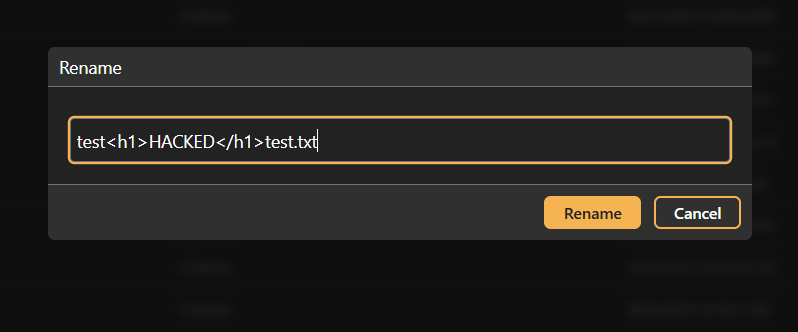
3. Click on "Rename" and rename the file to:
```html
test<h1>HACKED</h1>test.txt
```
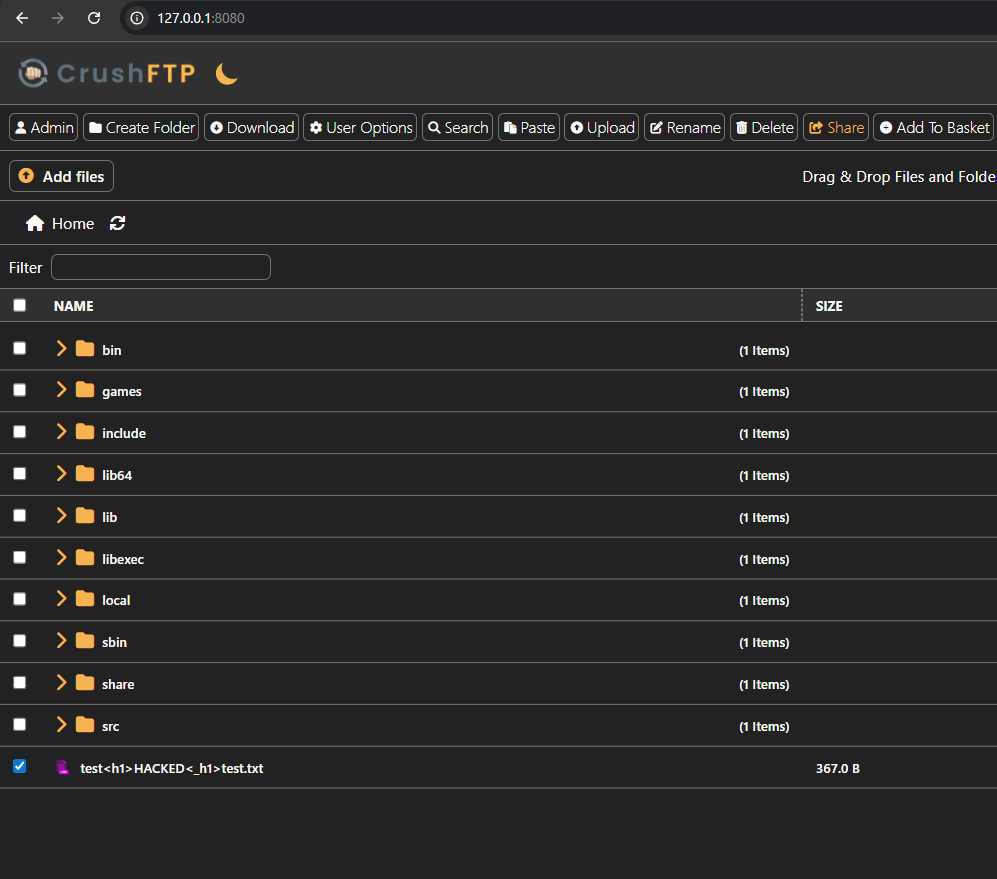
4. Select the file
5. Click on "Share" and observe the unintentional HTMLi:
# Credit
Muntadhar M. Ahmed ([almuntadhar0x01](https://almuntadhar0x01.me/)
[4.0K] /data/pocs/4d2349c1eb5949eac73c8d9146edb08d42269c98
└── [1.6K] README.md
1 directory, 1 file