This repository contains a Python script that checks WordPress websites for the CVE-2022-3590 vulnerability, which exploits an unauthenticated blind Server-Side Request Forgery (SSRF) in the WordPress pingback feature.# CVE-2022-3590 WordPress Vulnerability Scanner
This Python script is designed to check whether a WordPress website is vulnerable to the CVE-2022-3590 vulnerability. The vulnerability exploits an unauthenticated blind Server-Side Request Forgery (SSRF) in the pingback feature of WordPress.
## Getting Started
These instructions will guide you on how to use this script.
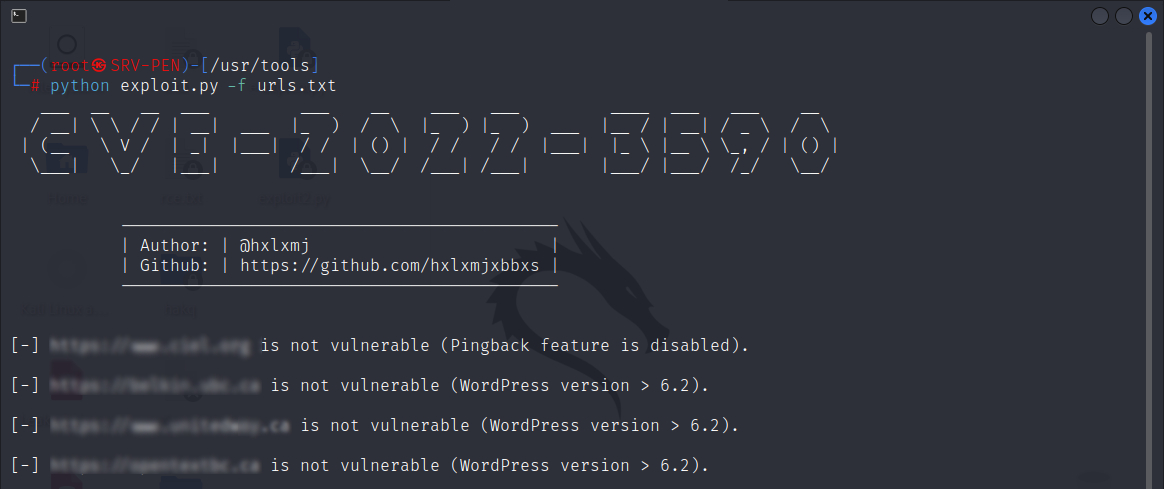
## Screenshot
### Prerequisites
This script requires Python 3 and the `requests` library. You can install the necessary requirements using pip:
```
pip install -r requirements.txt
```
### Usage
You can run the script from the command line with the following syntax:
```
python3 CVE-2022-3590.py [-u URL | -f FILE] [-d DOMAIN]
```
Here is what each argument does:
- `-u URL` or `--url URL`: The URL of the WordPress website to check.
- `-f FILE` or `--file FILE`: A file containing a list of URLs of WordPress websites to check.
- `-d DOMAIN` or `--domain DOMAIN`: The domain controlled by the attacker.
(You can use public.requestbin.com or app.interactsh.com)
### Example
To scan a single website:
```
python3 CVE-2022-3590.py -u https://example.com
```
To scan multiple websites from a file:
```
python3 CVE-2022-3590.py -f urls.txt
```
### Output
The script will output whether each scanned website is vulnerable to the CVE-2022-3590 vulnerability.
## License
This project is licensed under the MIT License.
## Acknowledgments
https://blog.sonarsource.com/wordpress-core-unauthenticated-blind-ssrf/
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-2745
https://wpscan.com/vulnerability/c8814e6e-78b3-4f63-a1d3-6906a84c1f11
https://blog.sonarsource.com/wordpress-core-unauthenticated-blind-ssrf/
[4.0K] /data/pocs/57056a37e045239fac4643e874ef11701deba857
├── [5.0K] CVE-2022-3590.py
├── [4.0K] img
│ └── [230K] cli.jpg
├── [1.0K] LICENSE
├── [1.8K] README.md
└── [ 50] requirements.txt
1 directory, 5 files