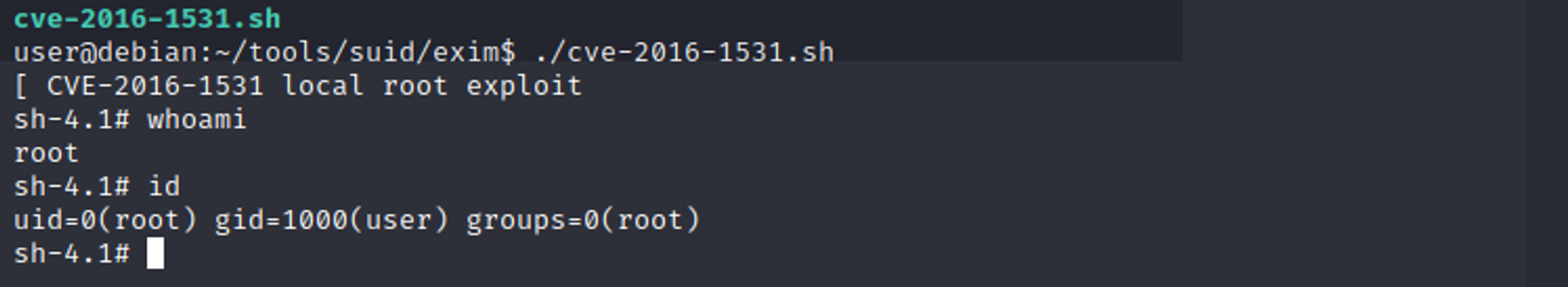
# CVE-2016-1531

[4.0K] /data/pocs/65facb25d3f3ead6daded37d4c2371ed88818404
├── [ 643] cve-2016-1531.sh
└── [ 243] README.md
0 directories, 2 files