Detect Citrix ADC SAML action or SAML iDP Profile config vulnerable to CVE-2020-8300 using Citrix ADC NITRO API
Detect Citrix ADC SAML action or SAML iDP Profile config vulnerable to CVE-2020-8300 using Citrix ADC NITRO API
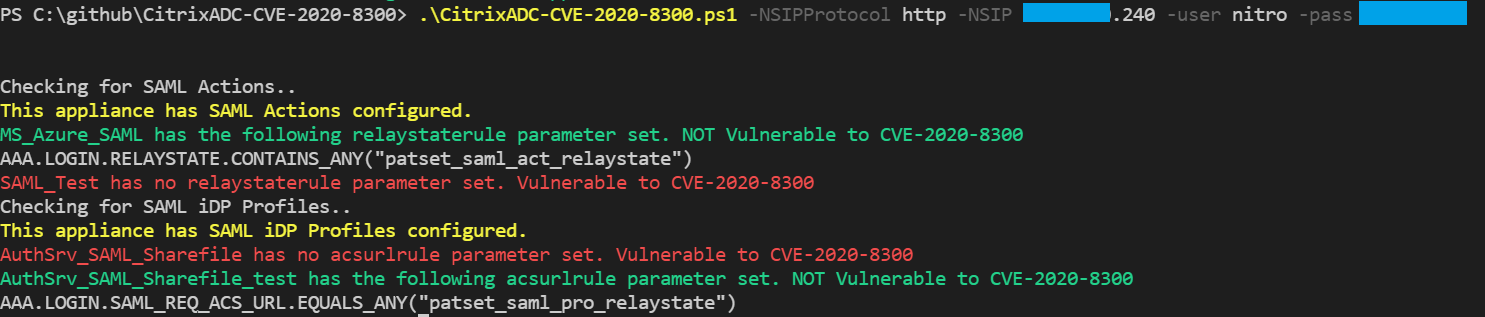
EXAMPLE
& '.\CitrixADC-CVE-2020-8300.ps1' -NSIPProtocol http -NSIP 10.10.10.10 -user nitro -pass "SshhhItsASecret"
If this proves useful to anyone I will develop further with the following functionality:
- Identify bindings for SAML Actions and SAML iDP Profiles to identify if and where they are in use
- Detect vulnerable firmware versions by seeing if the relaystaterule and acsurlrule parameters can be set
[4.0K] /data/pocs/710e7b66c1e1d62bbe5d46a07cfe715c7f87da45
├── [4.1K] CitrixADC-CVE-2020-8300.ps1
└── [ 642] README.md
0 directories, 2 files