关联漏洞
标题:CheckMK Raw Edition 跨站脚本漏洞 (CVE-2021-40906)Description:tribe29 CheckMK Raw Edition是德国tribe29公司的一个全面灵活的 IT 监控系统。 CheckMK Raw Edition 存在安全漏洞,该漏洞允许攻击者在设备上打开带有 HTML 内容并由浏览器解释(例如 JavaScript 或其他客户端脚本)的后门,或者窃取之前通过网络中的人进行身份验证的用户的会话 cookie。
介绍
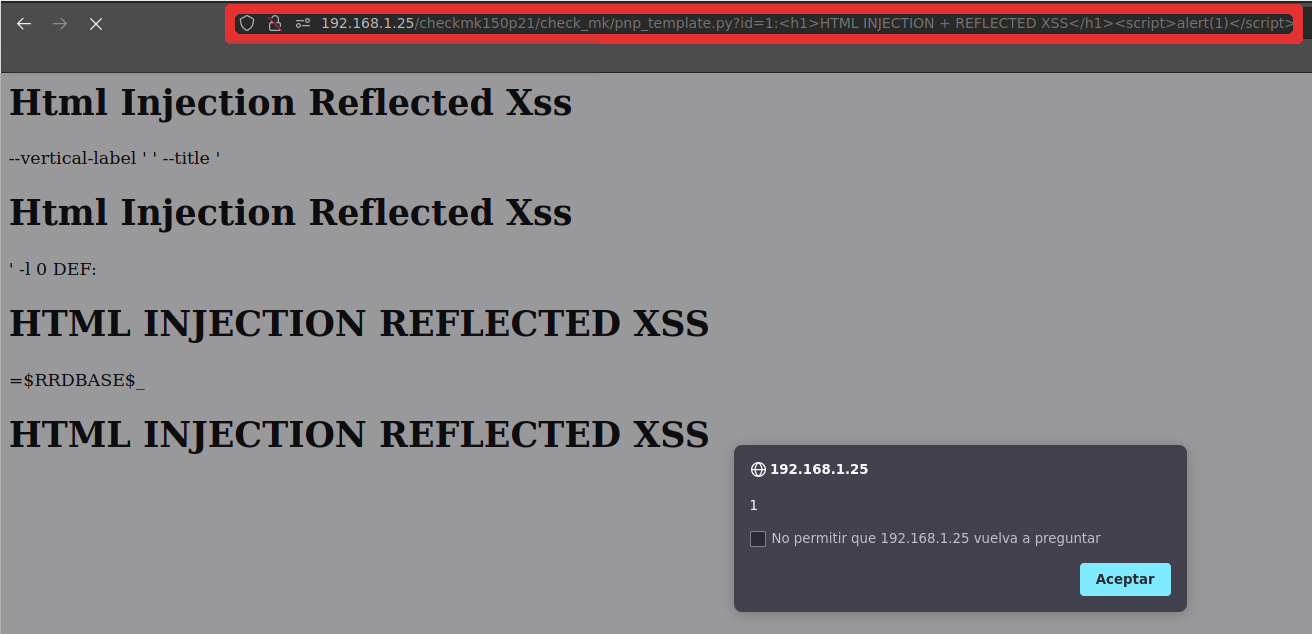
# CVE-2021-40906 - Reflected XSS in an unauthenticated zone
**Application:** CheckMK Management Web Console
**Software Revision:** From 1.5.0 to 1.5.0p25
**Author:** Edgar Augusto Loyola Torres.
**Attack type:** Reflected XSS
**Solution:** Update to Software Revision 1.6.0p26 or later
**Summary:** CheckMK Raw Edition software (versions 1.5.0 to 1.6.0) does not sanitise the input of a web service parameter that is in an unauthenticated zone. This Reflected XSS allows an attacker to open a backdoor on the device with HTML content and interpreted by the browser (such as JavaScript or other client-side scripts) or to steal the session cookies of a user who has previously authenticated via a man in the middle. Successful exploitation requires access to the web service resource without authentication.
**Technical Description:** See CVE-2021-40906
**Timeline:**
* 2021-09-01 Issues discovered.
* 2021-09-06 First contact with vendor via e-mail.
* 2021-09-08 Vendor response. XSS vulnerabilities were already detected, and would be patched in the next release.
* 2021-09-30 New Software Version release(1.6.0p27) and Vulnerability patch confirmed.
**Reference:**
* https://checkmk.com/werk/13192
* https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-40906
* https://nvd.nist.gov/vuln/detail/CVE-2021-40906
# DEMO
**PoC CheckMk version 1.5.0p25 Raw Edition**
文件快照
[4.0K] /data/pocs/87ad8e586518b2f513d4f9d0a2c09bbcbba9eb38
├── [1.5K] README.md
├── [473K] XSS-noAuth.pdf
└── [ 67K] XSS_no_auth.png
0 directories, 3 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。