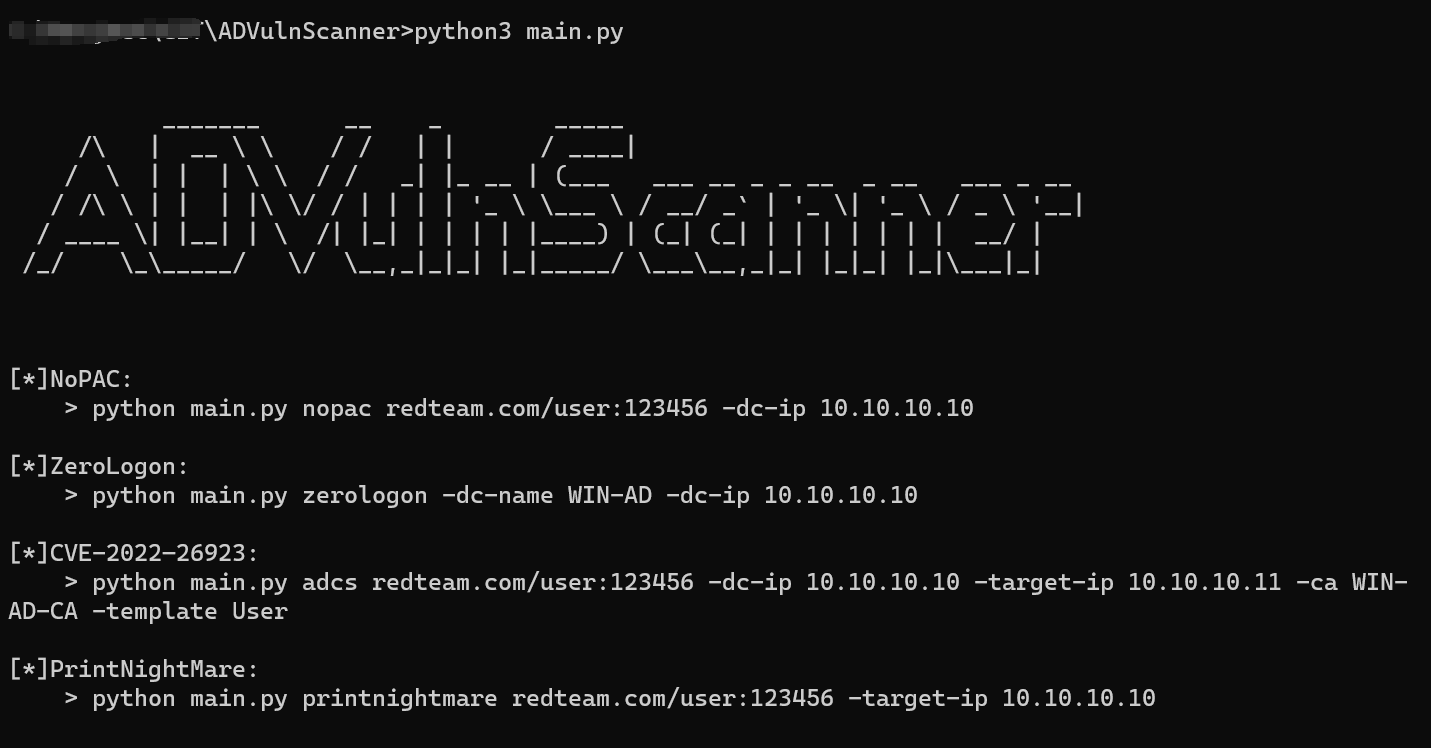
检测域内常见一把梭漏洞,包括:NoPac、ZeroLogon、CVE-2022-26923、PrintNightMare# ADVulnScanner
检测域内常见一把梭漏洞,包括:NoPac、ZeroLogon、CVE-2022-26923、PrintNightMare。
[4.0K] /data/pocs/88054c051278a314515e2692c85b2e11e5ccb16e
├── [4.0K] command
│ ├── [4.0K] adcs
│ │ ├── [ 34K] ca.py
│ │ ├── [ 27K] certificate.py
│ │ ├── [1.0K] options.py
│ │ ├── [4.0K] __pycache__
│ │ │ ├── [ 26K] ca.cpython-39.pyc
│ │ │ ├── [ 941] options.cpython-39.pyc
│ │ │ ├── [ 17K] req.cpython-39.pyc
│ │ │ └── [6.3K] template.cpython-39.pyc
│ │ ├── [ 25K] req.py
│ │ └── [8.3K] template.py
│ ├── [4.0K] nopac
│ │ ├── [ 11K] entry.py
│ │ └── [4.0K] __pycache__
│ │ └── [6.7K] entry.cpython-39.pyc
│ ├── [4.0K] printnightmare
│ │ ├── [5.5K] entry.py
│ │ ├── [3.1K] par_vector.py
│ │ ├── [4.0K] __pycache__
│ │ │ ├── [3.9K] entry.cpython-39.pyc
│ │ │ ├── [2.1K] par_vector.cpython-39.pyc
│ │ │ ├── [2.1K] rprn_vector.cpython-39.pyc
│ │ │ └── [1.1K] structs.cpython-39.pyc
│ │ ├── [3.2K] rprn_vector.py
│ │ └── [1.1K] structs.py
│ └── [4.0K] zerologon
│ ├── [4.8K] entry.py
│ └── [4.0K] __pycache__
│ └── [3.2K] entry.cpython-39.pyc
├── [7.3K] main.py
└── [ 235] README.md
9 directories, 23 files