关联漏洞
Description
Stored XSS vulnerability in Teampass < 3.0.9 (Bypass of CVE-2023–2516) — M Nadeem Qazi
介绍
# CVE-2023-3009
# Stored XSS on item name - Bypassing CVE-2023-2516 in TeamPass < 3.0.9 - by M Nadeem Qazi
## Description
This repository addresses the stored XSS vulnerability discovered in the nilsteampassnet/teampass application, which was assigned the CVE-2023-2516 identifier. The vulnerability can be exploited by creating two user accounts with access to the same folder. By generating a new item within the folder and inserting a payload XSS into the item's name, an attacker can trigger an XSS alert when the item is accessed. This bypasses the previous patch for CVE-2023-2516.
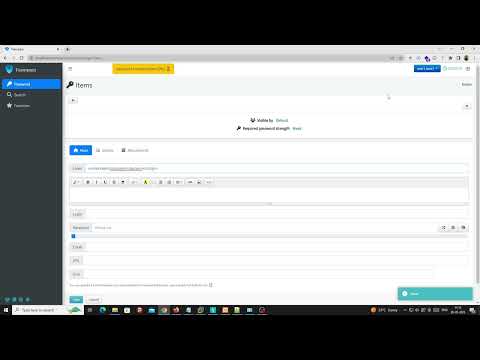
## Proof of Concept
A detailed proof of concept for this vulnerability can be found in video:
[](https://www.youtube.com/watch?v=T8tuqGGMRMY)
## Impact
The impact of this vulnerability is significant, as it allows an attacker to inject malicious code into a shared folder. Any users with access to the folder can then execute the injected code, leading to severe consequences such as data theft, unauthorized system access, and the potential for further attacks. This vulnerability enables attackers to compromise user credentials, compromise data confidentiality, gain control over victim accounts or devices, and propagate malware or ransomware throughout the network. If the shared folder is used for collaboration between multiple parties, the vulnerability can disrupt the entire group's work, resulting in loss of productivity and potential financial losses.
## Occurrences
The vulnerability can be observed in the `items.queries.php` file, specifically within lines L152-L1932.
## References
For more details on this vulnerability, please refer to the [huntr.dev report](https://huntr.dev/bounties/19470f0b-7094-4339-8d4a-4b5570b54716/).
or [Medium Blog - CVE-2023-3009](https://medium.com/@mnqazi/cve-2023-3009-stored-xss-vulnerability-in-teampass-3-0-9-45e8630ffb12)
You can also follow me for updates on my research and other security-related topics:
- Instagram: [@mnqazi](https://www.instagram.com/mnqazi)
- Twitter: [@mnqazi](https://twitter.com/mnqazi)
- Facebook: [@mnqazi](https://www.facebook.com/mnqazi)
- LinkedIn: [M_Nadeem_Qazi](https://www.linkedin.com/in/m-nadeem-qazi)
Stay safe out there!
文件快照
[4.0K] /data/pocs/8a7d59d09006b5f4aa62c52ab914a1b8ea3dcca8
└── [2.2K] README.md
0 directories, 1 file
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。