# CVE-2023-25292
Reflected Cross Site Scripting (XSS) in Intermesh BV Group-Office version 6.6.145, allows attackers to gain escalated privileges and gain sensitive information via the GO_LANGUAGE cookie
# Vulnerability Details
+ Product: Group Office Application
+ Version: 6.6.145
+ Vulnerability Type: Reflected XSS
+ Severity: High
+ CVSS v3 Score: 7.5 (AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N)
# Vulnerability Description
The application is vulnerable to a reflected XSS attack via the “GO_LANGUAGE” cookie that injects
malicious JavaScript into the application's response. The malicious script is executed in the context of
the affected website, allowing an attacker to steal sensitive information such as session cookies,
personal information, etc.
The vulnerability exists in the cookie of the Group Office application. By sending a specially crafted
cookie to the server, an attacker can inject malicious JavaScript code into the response, which is then
executed in the context of the affected website. This can result in sensitive information being stolen
from the user's browser, such as session cookies and personal information.
# Impact
This vulnerability allows an attacker to steal sensitive information from the affected website and its
users, such as session cookies, personal information, and more. An attacker can also use this
vulnerability to inject further malicious code into the affected website, compromising its functionality
and potentially exposing sensitive information.
# Remediation for the vendor
+ Filter input data to prevent malicious payloads from being included in the response.
+ Use a Content Security Policy (CSP) to restrict the execution of untrusted JavaScript in the
response.
+ Escape or encode all user input before including it in the response.
# Remediation for the end user
+ Upgrade to version 6.6.147 of the Group Office application.
# Steps to Reproduce
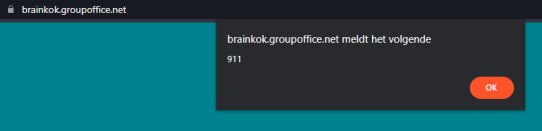
1. Go to the vulnerable instance of group-office.
2. Change the “GO_LANGUAGE” cookie with F12, to the following payload:
```
ar'"()&%<zzz><ScRiPt>alert(911)</ScRiPt>
```

3. Reload the page and then you will see that the payload is executed.
# References
+ https://github.com/Intermesh/groupoffice/blob/master/CHANGELOG.md
+ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-25292
[4.0K] /data/pocs/992c96e2f260472687251becfeffe75107169e11
└── [2.5K] README.md
0 directories, 1 file