CVE-2022-43096
CVSS v3.1 Vector: AV:P/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:N (7,3)
[Description]
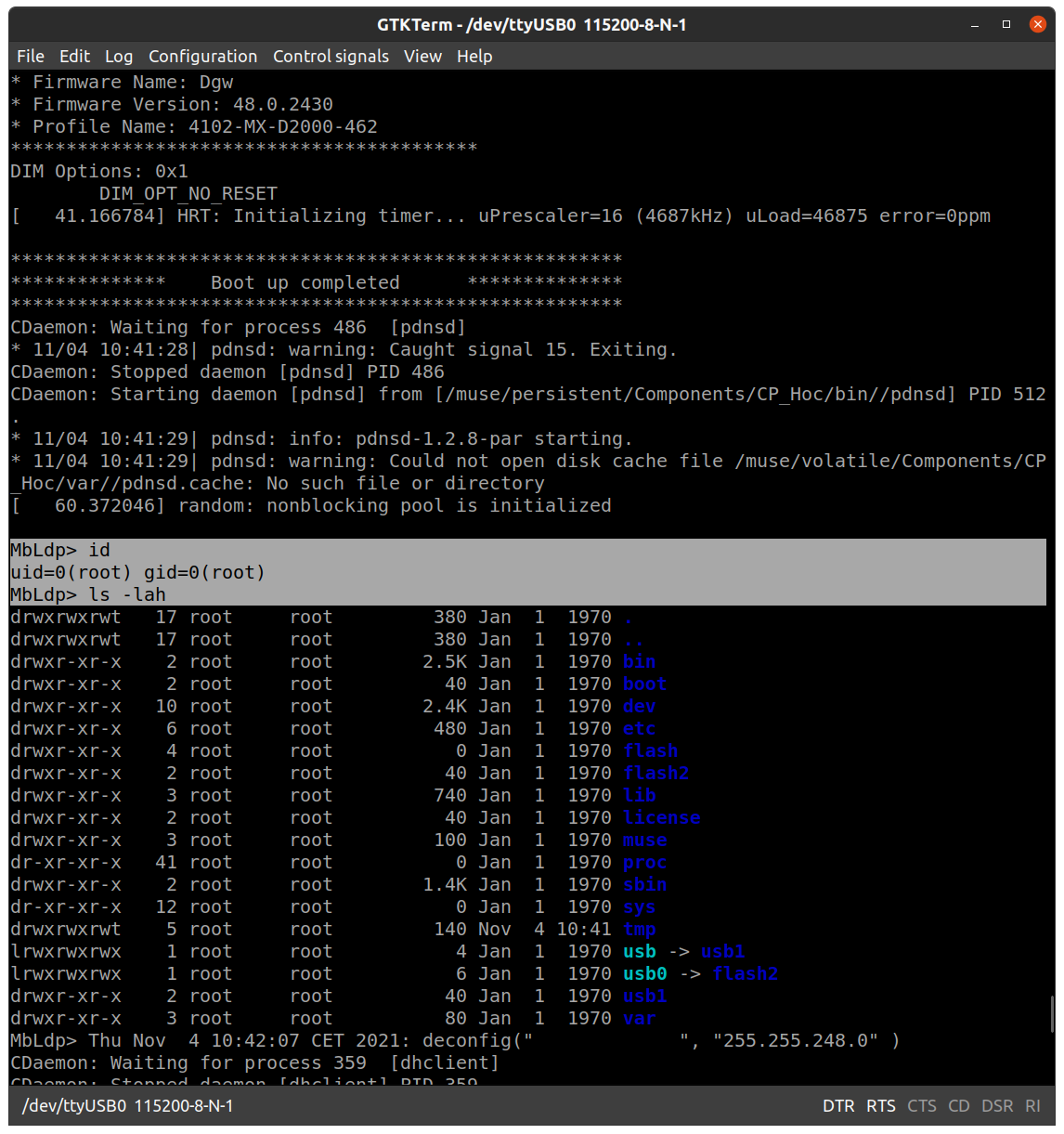
Mediatrix 4102 before v48.5.2718 allows local attackers to gain root
access via the UART port.
------------------------------------------
[Vulnerability Type]
Incorrect Access Control
------------------------------------------
[Vendor of Product]
Mediatrix
------------------------------------------
[Affected Product Code Base]
Mediatrix 4102 - Before v48.5.2718
------------------------------------------
[Affected Component]
UART port
------------------------------------------
[Attack Type]
Physical
------------------------------------------
[Impact Code execution]
true
------------------------------------------
[Impact Escalation of Privileges]
true
------------------------------------------
[Impact Information Disclosure]
true
------------------------------------------
[Reference]
Summary ID: DGW-15338
https://documentation.media5corp.com/display/MP/DGW+Security+Improvement+Notes+v48.5.2718
Product page:
https://www.m5t.com/products/mediatrix-access-devices/4100-voip-adaptors/
------------------------------------------
[Has vendor confirmed or acknowledged the vulnerability?]
true
------------------------------------------
[Discoverer]
Daniel Wong
[4.0K] /data/pocs/99fc5d10d05009fb976779ae55f85b501e44f1b7
└── [1.4K] README.md
0 directories, 1 file