PoC Script for CVE-2022-36553: Exploits an unauthenticated remote command injection vulnerability in Hytec Inter HWL-2511-SS device.# CVE-2022-36553 - Hytec Inter HWL-2511-SS Unauthenticated Remote Command Injection.
## Overview
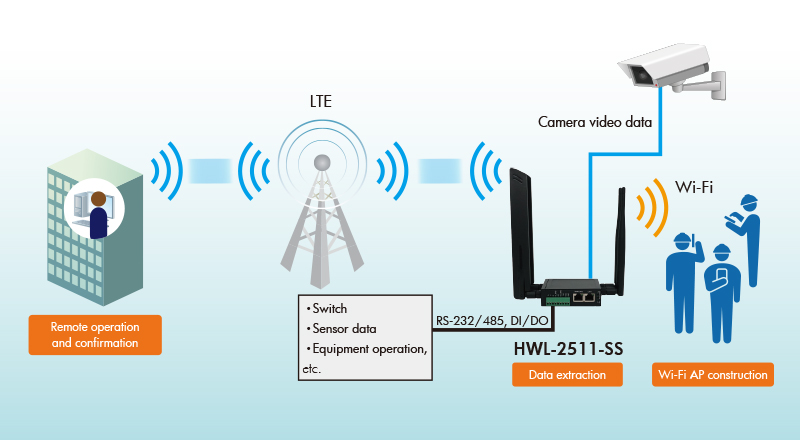
This repository contains a Proof of Concept (PoC) reverse shell script for exploiting CVE-2022-36553, a critical vulnerability in Hytec Inter HWL-2511-SS devices. The script is a practical demonstration, complementing the in-depth analysis provided in my blog post "Hytec Inter HWL-2511-SS - Vulnerability Report."
### Affected versions
All Hytec Inter HWL-2511-SS devices from version 1.05 and under.
### PoC Script Usage
```python
# Usage: python HWL-2511-SS.py --RHOST <Target-IP> --RPORT <Target-Port> --LHOST <Local-IP> --LPORT <Local-Port>
# Example: python HWL-2511-SS.py --RHOST 192.168.1.1 --RPORT 443 --LHOST 192.168.1.100 --LPORT 4444
```
### Video Proof of Concept
[](https://youtu.be/ILBJglgD-9U)
### Note
FOR EDUCATIONAL PURPOSE ONLY.
[4.0K] /data/pocs/9c8f30d06ffa580e9ef7a575b01c2c548cd6e2ab
├── [5.9K] HWL-2511-SS.py
└── [1.1K] README.md
0 directories, 2 files