Local Privilege Escalation Vulnerability on Axigen for Windows# CVE-2024-28589
A vulnerability has been discovered in Axigen Mail Server for Windows, affecting all versions up to 10.5.18, which allows for local privilege escalation.
### Description:
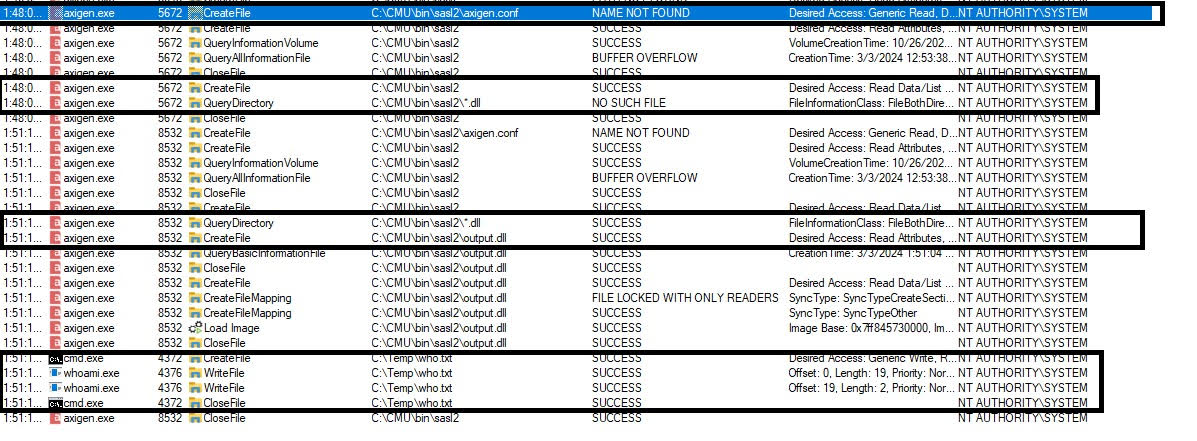
The Axigen Mail Server was found to be vulnerable to a local privilege escalation due to insecure DLL loading from a world-writable directory. During the service initiation of "Axigen Mail Server," which operates with SYSTEM privileges, it searches for a non-existent directory. An attacker with local access can create this directory and place a malicious DLL file in it. When the service starts, it attempts to load all DLL files in this directory, allowing the attacker's code to execute with SYSTEM privileges.
### Affected versions
Axigen 10.x up to 10.5.18
fixed starting with 10.5.19
### Impacted service(s)
Service Name: Axigen Mail Server
### DLL loaded from world-writable directory
#### Discovered by:
* Alaa Kachouh
* Ali Jammal of Deloitte Netherlands
[4.0K] /data/pocs/aca194d0f76976f5365a15da591a7f85c8252ac7
├── [166K] DLL-load.jpg
└── [1.0K] README.md
0 directories, 2 files