关联漏洞
标题:Microsoft SharePoint 输入验证错误漏洞 (CVE-2020-0976)Description:Microsoft SharePoint是美国微软(Microsoft)公司的一套企业业务协作平台。该平台用于对业务信息进行整合,并能够共享工作、与他人协同工作、组织项目和工作组、搜索人员和信息。 Microsoft SharePoint Enterprise Server 2016和Microsoft SharePoint Foundation 2013 SP1中存在安全漏洞。攻击者可通过向受影响的SharePoint服务器发送特制的请求利用该漏洞实施跨站脚本攻击并在当前用户的安全上下文中运行脚本。以下
介绍
# GUI Check CVE-2020-0796
#### 勘误:
正确的CVE名称是CVE-2020-0796,而不是CVE-2020-0976。此程序不改了,知道就好的。
#### Information
```
Microsoft SMBv3 contains a vulnerability in the handling of compression, which may allow a remote,unauthenticated attacker to execute arbitrary code on a vulnerable system.Microsoft Server Message Block 3.1.1 (SMBv3) contains a vulnerability in the way that it handles connections that use compression.
This vulnerability may allow a remote, unauthenticated attacker to execute arbitrary code on a vulnerable system.It has been reported that this vulnerability is "wormable."
By connecting to a vulnerable Windows machine using SMBv3, or by causing a vulnerable Windows system to initiate a client connection to a SMBv3 server,a remote, unauthenticated attacker to execute arbitrary code with SYSTEM privileges on a vulnerable system.
```
#### Infected system
```
+ Windows 10 Version 1903 for 32-bit Systems
+ Windows 10 Version 1903 for ARM64-based Systems
+ Windows 10 Version 1903 for x64-based Systems
+ Windows 10 Version 1909 for 32-bit Systems
+ Windows 10 Version 1909 for ARM64-based Systems
+ Windows 10 Version 1909 for x64-based Systems
+ Windows Server, version 1903 (Server Core installation)
+ Windows Server, version 1909 (Server Core installation)
```
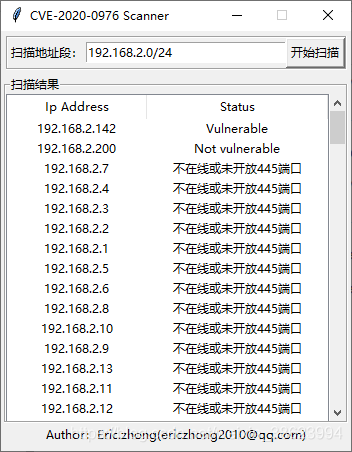
#### Snapshots
#### Workaround
1. CVE-2020-0796 Patch
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0796
2. Disable SMBv3 compression
```
Set-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters" DisableCompression -Type DWORD -Value 1 -Force
```
文件快照
[4.0K] /data/pocs/cd52edf4a84bae52169be3f26a04b65d0256e346
├── [6.2K] CVE-2020-0976.py
├── [1.9K] README.md
└── [4.0K] Windows
└── [7.7M] CVE-2020-0976.exe
1 directory, 3 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。